Author: Larry Fitzgerald & Bill Hawk | March 14, 2023
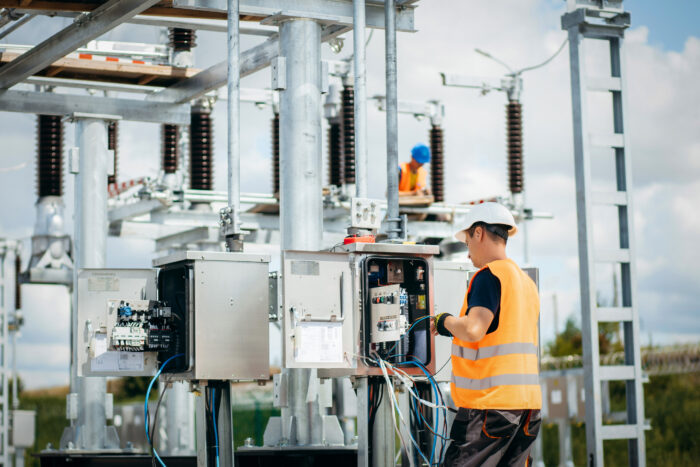
The Federal Energy Regulatory Commission (FERC) recently directed the North American Electric Reliability Corporation (NERC) to develop and submit for approval any new or modified Reliability Standards that require electric utilities to implement Internal Network Security Monitoring (INSM) within their trusted Critical Infrastructure Protection (CIP) environments. This requirement will apply to all High Impact bulk electric system (BES) Cyber Systems with and without external connectivity and to Medium Impact BES Cyber Systems with external connectivity.
The new standards will require that utilities develop baselines of the traffic inside their BES networked environments to monitor for and detect unauthorized activity, connections, devices and software.
Utilities must also identify anomalous activity to a higher level of confidence by logging network traffic, maintaining data and implementing measures to minimize the likelihood of an attacker removing evidence of their tactics, techniques and procedures from compromised devices.

What is Internal Network Security?
Internal network security refers to the implementation and monitoring of security measures within an organization’s trusted network environments, designed to detect intrusions and malicious activity. This encompasses the collection, detection, and analysis of network traffic, as well as the use of tools such as anti-malware, firewalls, and intrusion prevention systems. The goal is to maintain visibility over communications between networked devices and provide an additional layer of defense against cyber attacks.
Why INSM?
INSM is designed to alarm, as early as possible, in situations where the perimeter network defenses are breached by detecting intrusions and unusual or malicious activity within a trust zone.
INSM consists of three stages: (1) collection; (2) detection; and (3) analysis. Some of the tools that may be used for INSM include:
- Anti-malware software
- Intrusion detection systems
- Intrusion prevention systems
- Firewalls
These tools can be used for forensic investigation (e.g., collection, detection and analysis) of potential intrusive events. Additionally, some of the tools (anti-malware, firewall, or intrusion prevention systems) have the capability to block inappropriate or malicious network traffic.
According to FERC, INSM will better position a utility to detect malicious activity that has circumvented perimeter controls and gained access to the target systems.
Because an attacker that moves among devices internal to a trust zone must use network pathways and required protocols to send malicious communications, INSM can help alert a utility of the attack in its early phases and improve the utility’s ability to stop the attack and mitigate damages.

NERC Compliance News From TRC
Get the Latest Updates! Frequently changing regulatory requirements can impact your power engineering, design and compliance related processes in both the near and long term.
What Will Be Required in an INSM Standard?
According to FERC, INSM is a component of a comprehensive cybersecurity strategy because it provides an additional layer of defense against malicious intrusions regardless of the attack vector or whether existing security controls failed. With INSM, a utility can maintain visibility over communications between networked devices within a trust zone and detect malicious activity that has circumvented perimeter controls.
Currently, network security monitoring required by NERC’s CIP Reliability Standards focuses on network perimeter defense by preventing unauthorized access at the electronic security perimeter. While the CIP Standards require monitoring of inbound and outbound internet communications at the electronic security perimeter, they do not require monitoring within trusted CIP-networked environments for BES Cyber Systems. This gap may permit vendors or individuals with authorized access to be considered secure and trustworthy but still be able to introduce a cybersecurity risk, as well as other attack vectors.
NERC has been directed to develop new or modified CIP Reliability Standards that require INSM for CIP-networked environments within all high-impact BES Cyber Systems with and without external routable connectivity and medium impact BES Cyber Systems with external routable connectivity.
FERC determined that requirements to implement INSM will fill the identified gap in the current suite of CIP Reliability Standards and improve the cybersecurity posture of the Bulk-Power System. Specifically, a requirement for INSM augments existing perimeter defenses by increasing network visibility, so that a utility may understand what is occurring in its CIP-networked environment, and thus improve its capability to detect potential compromises in a timely manner.
Next Steps
TRC recommends that utility clients review this latest order and begin the process of considering how they would modify their CIP related protocols, policies, and procedures to adapt to NERC’s work product which will be developed over the course of the next fifteen months.

Your Trusted Regulatory Advisor:
The forgoing FERC action is a significant regulatory event which will create a fundamental change in security processes by adding internal network monitoring to the existing security perimeter approach embedded in the NERC CIP standards. TRC closely follows the national and state regulatory trends in all regions of North America. Our approach to power system security, engineering, planning, design, construction and commissioning testing, balances solutions that incorporate industry reliability risk trends, mandatory reliability standard requirements, regulatory guidance, compliance obligations, best practices, operational goals, and budgets. With expertise in power system engineering, planning and operations, TRC supports public utilities and private energy providers in their efforts to stay ahead of the curve and to meet or exceed regulatory requirements as they evolve.
This regulatory update is provided as a service to TRC’s utility clients, helping to keep you informed of forward-looking issues that will impact your company’s electric system reliability risks along with related topics regarding regulatory developments to help you achieve your company’s business goals.
Sharing Our Perspectives
Our practitioners share their insights and perspectives on the trends and challenges shaping the market.

Jumpstart Utility Modernization with Lemur Asset Mapping
April 16, 2026
Discover how Lemur mobile mapping helps utilities modernize faster by extending ArcGIS Utility Network and work/asset management into the field, reducing fragile integrations, improving data quality, and de‑risking digital transformation.

2026 Megatrends Powering the Shift in India’s Utility Landscape
March 16, 2026
India’s power and utility sector is operating in the midst of a defining decade. In 2026, utilities are finding themselves at the intersection of accelerating demand, renewable scale-up, grid constraints, infrastructure modernization and rising expectations around reliability and affordability.

Best Practices for Connecting OT Systems with Modern IT Architectures
February 27, 2026
Discover best practices and five key strategies for utilities to seamlessly integrate OT systems with modern IT architectures, overcoming legacy challenges for operational efficiency and scalability.

2026 Megatrends Powering the Shift in the Utility Landscape
January 28, 2026
Every so often, an industry reaches an inflection point — one of those rare moments when change doesn’t just accelerate, it fundamentally redefines the path ahead. For the utility industry, 2026 is that moment.

Five Strategies to Improve Model Management for Utilities and ISOs/RTOs
January 23, 2026
Discover five practical strategies utilities, ISOs and RTOs can use to modernize model management, break down data silos and build a single, accurate system of record that supports reliable, compliant grid operations.

Enable Predictive Asset Maintenance with AI-Powered Solutions for Utilities
January 19, 2026
Enable AI-powered predictive maintenance with TRC’s remote sensing, computer vision and cloud solutions to reduce outages, enhance grid reliability and turn imagery into actionable asset intelligence for utilities.

Discover How to Transform Operations and Customer Engagement with AMI 2.0
October 23, 2025
Discover how AMI 2.0 transforms utility operations and customer engagement with real-time data, advanced analytics and robust grid-edge innovation.

Minimize Outage Risk and Improve Response. Welcome to the “Resiliency Bow Tie.”
August 27, 2025
Explore how the Resiliency Bow Tie method helps utilities tackle rising outage risks from aging infrastructure, climate extremes and cyber threats. Learn how this strategic framework promotes effective risk mitigation, improves response times and fosters cross-functional collaboration, enabling utilities to deliver reliable service.

Improve Data Quality and Reduce Costs with Accurate Field Capture
July 16, 2025
Discover how Lemur mobile mapping empowers utilities to improve data quality, streamline field operations and reduce costs. Lemur provides a unified, intuitive mobile solution that works online and offline, ensuring compliance and real-time decision-making.

The Transformative Benefits of 3D Facility Mapping for Utilities
June 26, 2025
Discover how modern 3D facility mapping empowers utilities to modernize infrastructure, improve asset management, and enable remote workflows with accurate digital twins, delivering cost savings and operational efficiency.

Grid Resiliency: Perspectives Across the Power Grid
April 16, 2025
In today’s changing energy landscape, grid resiliency is a top priority for all power system owners and operators. The ability to absorb disruptions and maintain power is crucial in an increasingly unpredictable world.

DERMS Part II: Take the Right Approach to Implementing DERMS
March 27, 2025
Implementing DERMS can come with challenges. By understanding the unique challenges related to DERMS and adopting the appropriate strategies to mitigate potential pitfalls, utilities can effectively integrate and coordinate DER deployment to align with regulatory commitments and broader business objectives.

How ISOs, RTOs and Utilities Can Effectively Manage Massive Data
March 20, 2025
In today’s rapidly evolving energy landscape, Independent System Operators (ISOs), Regional Transmission Organizations (RTOs) and utilities face unprecedented challenges in managing vast amounts of data.

DERMS Part I: How DERMS Delivers Modern Utility Management
February 5, 2025
Supercharges its leading position in the Power & Energy sector Milestone transaction: To welcome a U.S. premier Power & Energy brand of approximately 8,000 people to create the #1 Power & Energy platform in the U.S1 (total cash purchase price of US$3.3 billion). Highly accretive: Expected to be low- to mid-single digit percentage accretive to WSP’s adjusted net earnings per share2 and high-single digit percentage accretive once cost synergies are fully realized2,3 Highly complementary: To expand our offering in the Power & Energy sector and provide potential cross-selling opportunities similar to our POWER Engineers experience. Drives scale across strategic high-growth areas fueled by strong fundamentals: o Grows Advisory capabilities o Expands Program Management expertise o Adds to Digital offering with innovative solutions o Enhances service offering across Water, Infrastructure and Environment Elevates leading position in the U.S.: Combined with TRC, WSP will become the largest engineering and design firm in the U.S. by revenue4, with approximately 27,000 employees. Provides further diversification: 34% of U.S. net revenues to be derived from the Power & Energy sector.5 Accelerates WSP’s organic growth rate profile globally: Approximately two-thirds of WSP’s global net revenues to be derived from Canada and the Americas, and approximately 20% from Power & Energy—a double-digit organic growth rate sector.6 Fully aligned with WSP’s 2025-2027 Global Strategic Action Plan: Pioneering change for empowered growth. ~$850 million equity offering composed of $732 million bought deal and approximately $118 million concurrent private placement with La Caisse. NOT FOR RELEASE, PUBLICATION, OR DISTRIBUTION IN OR INTO THE UNITED STATES OF AMERICA OR TO ANY PERSON LOCATED OR RESIDENT IN THE UNITED STATES OF AMERICA, ITS TERRITORIES AND POSSESSIONS, ANY STATE OF THE UNITED STATES, OR THE DISTRICT OF COLUMBIA. BASE SHELF PROSPECTUS IS ACCESSIBLE, AND THE PROSPECTUS SUPPLEMENT WILL BE ACCESSIBLE WITHIN TWO BUSINESS DAYS, ON SEDAR+ MONTREAL, December 15, 2025 – WSP Global Inc. (TSX: WSP) (“WSP” or the “Corporation”), one of the world’s leading professional services firms, proudly announces it has entered into an agreement to acquire TRC Companies (“TRC”), a premier U.S. Power & Energy brand delivering end-to-end solutions that support the full infrastructure lifecycle (the “Acquisition”), currently majority-owned by funds managed by Warburg Pincus LLC. The proposed Acquisition, for a total cash purchase price of US$3.3 billion (approximately $4.5 billion based on the exchange rate of $1.3762 USD/CAD as of December 15, 2025), marks a significant step on WSP’s journey to achieve its 2025-2027 Global Strategic Action Plan. The proposed Acquisition will position WSP as the largest engineering and design firm in the U.S., supercharging its Power & Energy offering and enhancing its capabilities across Water, Infrastructure, and Environment. Based in Windsor, Connecticut, TRC has been a pioneer in adaptability and innovation for more than 55 years. TRC has established itself as a leader and recognized strategic advisor in the engineering and consulting industry, maintaining deep, long-term relationships with blue-chip utilities. Its team of approximately 8,000 employees offers an integrated approach that delivers long-term value for clients facing complex infrastructure and energy challenges. The proposed Acquisition complements WSP’s offering in attractive market sectors, will expand its client relationships, and enhance its capabilities throughout the project lifecycle, notably with a portfolio of advisory practices tailored to utilities and program management expertise. It will also create potential cross-selling opportunities across power engineering, environmental solutions, and advisory services. At the same time, TRC will bring a shared commitment to innovation and operational excellence, with investments in digital solutions and a highly skilled workforce—further amplifying WSP’s ability to deliver integrated, future-forward solutions. “The proposed Acquisition of TRC is a defining moment in the execution of WSP’s 2025-2027 Strategic Plan. Building on our track record of excellence and compounding financial performance, this strategic move will cement WSP as the Power & Energy consulting leader in the U.S. and globally. Joining forces will position our business for accelerated organic growth and create an integrated platform with industry-leading capabilities in advisory, engineering, and program management. With TRC’s highly complementary expertise in power delivery, transmission, distribution, and advisory services, our combined offering will cover the entire utility and infrastructure value chain. Together, we are poised to deliver more complex projects and offer expanded end-to-end services to help solve our clients’ critical needs, from aging infrastructure to grid modernization and electrification,” commented Alexandre L’Heureux, President and Chief Executive Officer of WSP. Also commenting on the Acquisition, Christopher P. Vincze, Chairman and Chief Executive Officer of TRC, said: “The joining of our two firms will create significant and exciting opportunities for our people, our clients and the communities in which we live and work. With TRC’s innovative, technology-oriented power business, underscored by an advanced use of digital, we will significantly strengthen WSP’s Power & Energy offering. Additionally, TRC’s globally recognized Environmental & Infrastructure business, which is the seed from which TRC grew, will enhance WSP’s capabilities across Water, Infrastructure and Environment. Our combined skill sets will elevate us to better support, over the next decade and beyond, our people and planet as we face unprecedented growth of power needs on the back of ongoing electrification, the re-emergence of domestic manufacturing in the U.S. and the continued growth of infrastructure. We were an early pioneer in the utility sector and continue to be a trusted thought partner, working to create, implement and manage complex strategies and programs to meet the country’s power needs. TRC’s people continue to be passionate about making the world a better place, and this next chapter will allow us to come together with WSP in a very exciting way to further that goal.” Reflecting on their investment, Kim Thomassin, Executive Vice President and Head of Québec at La Caisse said: “With this investment, La Caisse once again demonstrates its ongoing commitment to WSP, helping to position the company as a leader in engineering and design in the United States and globally, while accelerating the development of its Energy offering, a sector with strong potential. This transaction is at the core of our strategy to support the international expansion of companies firmly rooted in Québec and to give them the means to achieve sustainable growth.” FINANCIAL HIGHLIGHTS Proposed Acquisition of TRC for a total cash purchase price of US$3.3 billion approximately $4.5 billion based on the exchange rate of $3762 USD/CAD as of December 15, 2025). Acquisition price represents 14.5x TRC’s Pre-IFRS 16 CY2026E Adjusted EBITDA6 pre-synergies and 12.5x after including run-rate synergies.8 (TRC’s Pre-IFRS 16 Adjusted EBITDA and earnings before net interest and income tax for the financial year ended June 30, 2025 were approximately US$192.3 million ($268.5 million) and US$87.5 million ($122.1 million), respectively). Expected to be low-to-mid single-digit percentage accretive to WSP’s adjusted net earnings per share before synergies. WSP expects 2027 Accretion (as defined below) to be high single-digit percentage accretive once cost synergies are fully realized (WSP’s basic net earnings per share attributable to shareholders and adjusted net earnings per share were $5.40 and $8.05 respectively, for the financial year ended December 31, 2024).2,9 Expected cost synergies to exceed 3% of TRC’s net revenues for the financial year ended June 30, 20257, plus potential cross-selling revenue synergy opportunities in alignment with our POWER Engineers experience (TRC’s net revenues and revenues for the financial year ended June 30, 2025 were approximately US$1,192.2 million and US$1,498.9 million, respectively). Transaction to be financed with US$3.3 billion of Committed Acquisition Financing (as defined below). Estimated pro forma Net Debt to Adjusted EBITDA ratio6 of ~2.4x upon closing of the Acquisition with the expectation to return to below 2.0x within 12 months6 (WSP’s net debt to adjusted EBITDA ratio for the nine-month period ended September 27, 2025 was 1.4x and adjusted EBITDA and earnings before net financing expense and income taxes for the trailing twelve-month period ended September 27, 2025 were approximately $2,501.4 million and $1,481.0 million, respectively).8 Equity raise of approximately $850 million: $732 million bought deal public offering and approximately $118 million private placement of common shares of WSP (“Common Shares”) expected to close on or about December 22, 2025, with a corresponding reduction of the amounts drawn from the Committed Acquisition Financing. WSP may also opportunistically access debt capital markets to repay a further portion of the Committed Acquisition Financing should market conditions be favourable. WEBCAST WSP will host a webcast today at 4:45 p.m. (Eastern Daylight Time) to discuss the Acquisition. Exceptionally, there will be no question-and-answer session, given the concurrent equity offering. To join the webcast, please register at https://www.icastpro.ca/rp92yd or access https://www.wsp.com/en-gl/investors. A presentation of the Acquisition is accessible on the webcast platform and under the “Investors” section of WSP’s website. CONDITIONS TO THE ACQUISITION Subject to the satisfaction of certain customary closing conditions, including applicable regulatory approvals, the Acquisition is expected to be completed in the first quarter of 2026. ACQUISITION FINANCING Equity Financing The Equity Financing (as defined below) comprises: $732 million bought deal public offering (the “Offering”) of common shares (the “Offering Common Shares”) at a price of $232.80 per Offering Common Share (the “Offer Price”); and Approximately $118 million private placement (the “Concurrent Private Placement” and together with the Offering, the “Equity Financing”) of common shares (the “Placement Common Shares”) at the Offer Price to Caisse de dépôt et placement du Québec (“La Caisse”) WSP intends to use the net proceeds from the Equity Financing to fund in part the purchase price payable in respect of the Acquisition (and related costs and expenses) and accordingly reduce amounts to be drawn on the closing of the Acquisition under the Committed Acquisition Financing to fund the purchase price for the Acquisition. Public Offering WSP has entered into an agreement with CIBC Capital Markets, BMO Capital Markets and National Bank Capital Markets (the “Joint Bookrunners”), on behalf of a syndicate of underwriters (the “Underwriters”), to issue and sell, on a “bought deal” basis, 3,145,000 Offering Common Shares at the Offer Price for gross proceeds to the Corporation of $732 million. The Corporation has granted the Underwriters an over-allotment option (the “Over-Allotment Option”), exercisable in whole or in part, for a period of 30 days following the date of the closing of the Offering to purchase up to an additional number of Offering Common Shares equal to 15% of the Offering Common Shares to be sold pursuant to the Offering at the Offer Price to cover over-allotments, if any, and for market stabilization purposes. The Offering Common Shares distributed pursuant to the Offering will be offered in all provinces and territories of Canada pursuant to a prospectus supplement (the “Prospectus Supplement”) to the short form base shelf prospectus of WSP dated August 8, 2024 (the “Base Shelf Prospectus”) to be filed by WSP on or about December 17, 2025, as well as in the United States by way of private placement to “qualified institutional buyers” in reliance upon the exemption from registration provided by Rule 144A under the U.S. Securities Act of 1933, as amended (the “1933 Act”). The completion of the Offering is subject to the approval of the Toronto Stock Exchange (the “TSX”). Closing of the Offering is expected to occur on or about December 22, 2025 and is conditional upon the concurrent completion of the Concurrent Private Placement. No securities regulatory authority has either approved or disapproved the contents of this press release. The Offering Common Shares have not been, and will not be, registered under the 1933 Act, or any state securities laws. Accordingly, the Offering Common Shares may not be offered or sold within the United States unless registered under the 1933 Act and applicable state securities laws or pursuant to exemptions from the registration requirements of the 1933 Act and applicable state securities laws. This press release shall not constitute an offer to sell or the solicitation of an offer to buy securities in the United States, nor shall there be any sale of the Offering Common Shares in any jurisdiction in which such offer, solicitation or sale would be unlawful. Delivery of the Prospectus Supplement, and any amendments to the documents will be provided in accordance with securities legislation relating to procedures for providing access to a shelf prospectus supplement, and any amendment. The Prospectus Supplement will be (within two business days of the date hereof) accessible on SEDAR+ at www.sedarplus.ca. An electronic or paper copy of the Prospectus Supplement, and any amendment to the documents, may be obtained without charge from CIBC Capital Markets at 161 Bay Street, 5th Floor, Toronto, ON M5J 2S8 or by telephone at 1-416-956-6378 or by email at mailbox.Canadianprospectus@cibc.com by providing the contact with an email address or address, as applicable. The Prospectus Supplement contains important, detailed information about the Corporation and the proposed Offering. Prospective investors should read the Prospectus Supplement (when filed) before making an investment decision. Concurrent Private Placement Concurrently with this announcement, WSP has also entered into a subscription agreement pursuant to which the Corporation will complete the Concurrent Private Placement at the Offer Price with La Caisse for aggregate gross proceeds to the Corporation of approximately $118 million. La Caisse has also been granted an option (the “Additional Subscription Option”) to purchase a number of additional Placement Common Shares representing up to 15% of the number of Placement Common Shares subscribed by them on closing, subject to, and in the same proportion as the Over-Allotment Option being exercised by the Underwriters. The issuance of the Placement Common Shares under the Concurrent Private Placement is subject to the approval of the TSX. Closing of the Concurrent Private Placement is scheduled to occur concurrently with the closing of the Offering and is conditional upon the concurrent completion of the Offering. Assuming completion of the Concurrent Private Placement and the Offering, but not the exercise of the Over-Allotment Option or the Additional Subscription Option, La Caisse will beneficially own, or exercise control or direction over, directly or indirectly, an aggregate of 18,619,100 Common Shares representing approximately 13.9% of the then issued and outstanding Common Shares. The Placement Common Shares will be subject to a four month hold from the closing date of the Concurrent Private Placement. In accordance with the terms of the Subscription Agreement, the Placement Common Shares will also be subject to contractual lockups for a period of four (4) months following the date of issuance of such Placement Common Shares. La Caisse (or their respective designee) will be entitled to a capital commitment fee equal to 4% of the aggregate purchase price for the Placement Common Shares for which they have subscribed (and any additional Placement Common Shares they have subscribed pursuant to the Additional Subscription Option, as applicable). Committed Acquisition Financing Concurrently with the announcement of the Acquisition, Canadian Imperial Bank of Commerce and JP Morgan Chase Bank, N.A., acting as co-lead arrangers and joint bookrunners, provided commitments for US$3,300 million senior unsecured non-revolving term loans (collectively, the “Committed Acquisition Financing”). The Committed Acquisition Financing will be governed by an incremental facility supplement to the Corporation’s seventh amended and restated credit agreement dated as of April 27, 2023, as amended and supplemented from time to time, with a syndicate of financial institutions to be entered into on or before the closing of the Acquisition. All of the above elements of the Acquisition financing plan have been designed and structured with a view to preserving WSP’s investment grade rating. Related Party Transaction Matters La Caisse beneficially owns, or has control or direction over, directly or indirectly, Common Shares representing more than 10% of the issued and outstanding Common Shares of WSP. As a result of the foregoing, the Concurrent Private Placement is a “related party transaction” for the purposes of Multilateral Instrument 61-101 – Protection of minority security holders in special transactions (“MI 61-101”). The Corporation has relied on the exemptions from the valuation and minority approvals of MI 61-101 contained in paragraphs 5.5(a) and 5.7(a) of MI 61-101 on the basis that neither the fair market value of the Concurrent Private Placement (including the capital commitment fee payable thereunder), nor the consideration thereof, exceeds 25% of the market capitalization of the Corporation. FINANCIAL AND LEGAL ADVISORS JP Morgan and CIBC Capital Markets are acting as financial advisors to WSP on the Acquisition. Legal advice is being provided to WSP by Skadden, Arps, Slate, Meagher & Flom LLP in the United States and Stikeman Elliott LLP in Canada. Harris Williams, UBS Investment Bank, AEC Advisors, and Houlihan Lokey are acting as financial advisors to TRC on the Acquisition. Legal advice is being provided to TRC by Paul, Weiss, Rifkind, Wharton & Garrison LLP. About TRC TRC stands for adaptability. With direction setting perspectives and partnerships, our 8,000+ tested practitioners in advisory, consulting, construction, engineering and management services deliver unique resolutions that answer any built or natural imperative. By creating new pathways for the world to thrive, we help our clients adapt to change and achieve long-lasting results while solving the challenges of making the Earth a better place to live — community by community and project by project. TRC is ranked #17 on ENR’s list of the Top 500 Design Firms, #5 for Power and #3 for Transmission & Distribution. Learn more at TRCcompanies.com and follow us on LinkedIn. About La Caisse At La Caisse, formerly CDPQ, we have invested for 60 years with a dual mandate: generate optimal long term returns for our 48 depositors, who represent over 6 million Quebecers, and contribute to Québec’s economic development. As a global investment group, we are active in the major financial markets, private equity, infrastructure, real estate and private credit. As at June 30, 2025, La Caisse’s net assets totalled CAD 496 billion. For more information, visit lacaisse.com or consult our LinkedIn or Instagram pages. La Caisse is a registered trademark of Caisse de dépôt et placement du Québec that is protected in Canada and other jurisdictions and licensed for use by its subsidiaries. About WSP WSP is one of the world’s leading professional services firms, uniting its engineering, advisory and science-based expertise to shape communities to advance humanity. From local beginnings to a globe-spanning presence today, WSP operates in over 50 countries and employs approximately 75,000 professionals, known as Visioneers. Together they pioneer solutions and deliver innovative projects in the transportation, infrastructure, environment, building, energy, water, and mining and metals sectors. WSP is publicly listed on the Toronto Stock Exchange (TSX:WSP). FORWARD-LOOKING STATEMENTS Certain information contained herein is not based on historical facts and may constitute forward-looking statements or forward-looking information under Canadian securities laws (collectively, “forward-looking statements”). Forward-looking statements may include estimates, plans, strategic ambitions, objectives, expectations, opinions, forecasts, projections, guidance, outlook, expectations regarding the requirements of various end markets, demand for and investments in power and energy related services and infrastructure, trends or other statements that are not statements of fact. Forward-looking statements made by the Corporation in this document may include statements about the Acquisition, the benefits, synergies and opportunities of the Acquisition, the Offering and the Concurrent Private Placement and the use of proceeds therefrom; the closing of the Offering and the Concurrent Private Placement; the conditions precedent to the closing of the Acquisition; the expected closing date of the Acquisition; the Committed Acquisition Financing, available liquidities, the attractiveness of the Acquisition from a financial perspective and expected accretion in various financial metrics (including estimated 2027 Accretion, Accretion Upon Closing of the Acquisition, TRC Pre-IFRS 16 Adjusted EBITDA and WSP’s Pro Forma Net Debt to Adjusted EBITDA ratio upon closing of the Acquisition and within 12 months following closing of the Acquisition); expectations regarding anticipated cost savings and synergies; the strength, complementarity and compatibility of TRC’s business with WSP’s existing business and teams; other anticipated benefits of the Acquisition and their expected impact on WSP’s delivery of its strategic plan and its long-term vision, future growth, results of operations, financial performance, business, prospects and opportunities, WSP’s business outlook, objectives, development, plans, integration, growth strategies and other strategic priorities, and WSP’s leadership position in its markets; and statements relating to WSP’s future growth, results of operations, performance business, prospects and opportunities, the expected synergies to be realized and certain expected financial ratios and other statements that are not historical facts. Forward-looking statements can typically be identified by terminology such as “may,” “will,” “should,” “expect,” “plan,” “anticipate,” “believe,” “estimate,” “predict,” “forecast,” “project,” “intend,” “target,” “potential,” “continue” or the negative of these terms or terminology of a similar nature. Such forward-looking statements reflect current beliefs of Management and are based on certain factors and assumptions, which by their nature are subject to inherent risks and uncertainties. While the Corporation considers these factors and assumptions to be reasonable based on information available as at the date hereof, actual events or results could differ materially from the results, predictions, forecasts, conclusions or projections expressed or implied in the forward-looking statements. Forward-looking statements made by WSP are based on a number of assumptions believed by WSP to be reasonable as at the date hereof, including assumptions set out through this document and including, without limitation, principal assumptions about the satisfaction of all closing conditions and the successful completion of the Offering and the Concurrent Private Placement within the anticipated timeframe; the expected timing of completion of the Acquisition and the conditions precedent to the closing of the Acquisition (including the receipt of regulatory approvals); WSP’s ability to retain and attract new business, achieve synergies and maintain market position arising from successful integration plans relating to the Acquisition; WSP’s ability to otherwise complete the integration of TRC within anticipated time periods and at expected cost levels; WSP’s ability to attract and retain key employees in connection with the Acquisition; Management’s estimates and expectations in relation to future economic and business conditions and other factors in relation to the Acquisition and resulting impact on growth and accretion in various financial metrics; Management’s expectations in relation to the future performance and economic conditions and other factors in relation to TRC; the realization of the expected strategic, financial and other benefits of the Acquisition in the timeframe anticipated; the accuracy and completeness of the information (including financial information) provided by TRC and publicly available information; the absence of significant undisclosed costs or liabilities associated with the Acquisition; general economic and political conditions; organic growth expectations; economic and market assumptions regarding competition; the state of the global economy and the economies of the regions in which WSP or TRC operates; the state of and access to global and local capital and credit markets; interest rates; working capital requirements; the collection of accounts receivable; WSP obtaining new contract awards; the type of contracts entered into by WSP; the anticipated margins under new contract awards; the adequate utilization of WSP’s workforce; the ability of WSP to attract new clients; the ability of WSP to retain current clients; changes in contract performance; project delivery; WSP’s competitors; the ability of the Corporation to successfully integrate businesses; the acquisition and integration of businesses in the future; WSP’s ability to manage growth; external factors affecting the global operations of WSP; the state of WSP’s backlog and pipeline of opportunities in various reportable segments; the joint arrangements into which WSP has entered or will enter; capital investments made by the public and private sectors; relationships with suppliers and subconsultants; relationships with management, key professionals and other employees of WSP; the maintenance of sufficient insurance; the management of environmental, social and health and safety risks; the sufficiency of the WSP’s current and planned information systems, communications technology and other technology; the sufficiency of the Corporation’s cybersecurity measures; compliance with laws and regulations; future legal proceedings; the sufficiency of internal and disclosure controls; the regulatory environment; impairment of goodwill; foreign currency fluctuation; the expected benefits of acquisitions and the expected synergies to be realized as a result thereof; the tax legislation and regulations to which WSP is subject and the state of WSP’s benefit plans, as well as the assumptions underlying the 2025 financial outlook set out in WSP’s press releases dated February 12, 2025, August 6, 2025 and November 5, 2025. If any of these assumptions prove to be inaccurate, WSP’s actual results could differ materially from those expressed or implied in forward-looking statements. In evaluating these forward-looking statements, investors should specifically consider various risk factors, which, if realized, could cause WSP’s actual results or events to differ materially from those expressed or implied in forward-looking statements. Such risk factors include, but are not limited to: risks and uncertainties relating to the dilutive effect of the Offering on holders of Common Shares; the fact that the declaration of dividends on the Common Shares is at the discretion of the board of directors of WSP; the fact that the price at which the Common Shares under the Offering are sold by the Underwriters may be less than the Offering Price; WSP’s inability to successfully integrate TRC’s business upon completion of the Acquisition; the possible delay or failure to close the Acquisition; the potential failure to realize anticipated benefits from the Acquisition; the potential failure to obtain regulatory approvals in a timely manner, or at all; the currency exchange risk and foreign currency exposure related to the purchase price payable in respect of the Acquisition; WSP’s reliance upon publicly available information and information provided by TRC in connection with, and for the purposes of, the Acquisition; risks associated with historical and pro forma financial information; potential undisclosed costs or liabilities associated with the Acquisition; WSP’s or TRC’s businesses being adversely impacted during the pendency of the Acquisition; and change of control and other similar provisions and fees, as well as other risk factors discussed in greater detail in section 20, “Risk Factors,” of WSP’s Management Discussion and Analysis for the fourth quarter and year ended December 31, 2024 and in section 17, “Risk Factors,” of WSP’s Management Discussion and Analysis for the third quarter and nine-month period ended September 27, 2025, and as may be supplemented from time to time in reports filed by the Corporation with securities regulators or securities commissions or other documents that the Corporation makes public, which are available on SEDAR+ at www.sedarplus.ca and which sections are incorporated herein by reference into this cautionary statement. Although we have attempted to identify important risk factors that could cause actual results or events to differ materially from those contained in forward-looking statements, there may be other risk factors not presently known to us or that we presently believe are not material that could also cause actual results or future events to differ materially from those expressed in such forward-looking statements. WSP cautions that the foregoing list of risk factors is not exhaustive and other unknown or unpredictable factors could have also a material adverse effect on the performance or results of WSP or TRC. Actual results and events may be significantly different from what we currently expect because of the risks associated with our business, industry and global economy and of the assumptions made in relation to these risks. As such, there can be no assurance that actual results will be consistent with forward-looking statements. The completion of the Acquisition is subject to customary closing conditions, termination rights and other risks and uncertainties, including, without limitation and as applicable, regulatory approvals, and there can be no assurance that the Acquisition will be completed. There can also be no assurance that if the Acquisition is completed, the strategic and financial benefits expected to result from the Acquisition will be realized. To the extent any forward-looking statement in this document constitutes financial outlook or future-oriented financial information within the meaning of applicable Canadian securities laws, such information is intended to provide investors with information regarding the Corporation, including the Corporation’s assessment of future financial plans, and may not be appropriate for other purposes. Financial outlook (including assumptions about future events, including economic conditions and proposed courses of action, based on the Corporation’s assessment of the relevant information currently available), as with forward-looking statements generally, is based on current estimates, expectations and assumptions and is subject to inherent risks and uncertainties and other factors. Any financial outlook or future oriented financial information included in this document has been prepared by, and is the responsibility of, Management. PricewaterhouseCoopers LLP, the independent auditor of the Corporation, has not audited, reviewed, examined, compiled nor applied agreed-upon procedures with respect to any such financial outlook or future-oriented financial information and, accordingly, PricewaterhouseCoopers LLP does not express an opinion with respect thereto. The PricewaterhouseCoopers LLP report incorporated by reference in the Prospectus Supplement relates to the Corporation’s previously issued financial statements for the financial year ended December 31, 2024. It does not extend to any financial outlook or future-oriented financial information and should not be read to do so. Differences could arise because of events announced or completed after the date of this press release. All of the forward-looking statements contained in this document are expressly qualified in their entirety by this cautionary statement. The forward-looking statements contained in this document are made as of the date hereof (unless otherwise specified) and, accordingly, are subject to change after such date. Except to the extent required by applicable law, WSP does not assume any obligation to publicly update or to revise any forward-looking statements made in this document or otherwise, whether as a result of new information, future events, or otherwise. Readers should not place undue reliance on forward-looking statements. Readers are also referred to cautionary language regarding forward-looking statements included in the Prospectus Supplement. Additional Underlying Assumptions The Corporation cautions that the assumptions used to prepare the estimated 2027 Accretion, Accretion Upon Closing of the Acquisition, TRC Pre-IFRS 16 Adjusted EBITDA, TRC Post-IFRS 16 Adjusted EBITDA, and WSP’s Pro Forma Net Debt to Adjusted EBITDA ratio upon closing of the Acquisition and within 12 months following closing of the Acquisition could prove to be incorrect or inaccurate. Accordingly, the actual results could differ materially from the Corporation’s expectations as set out in this press release. The Corporation considered numerous economic and market assumptions regarding the foreign exchange rate, competition, political environment, and economic performance of each region where the Corporation and TRC operate. In addition to the assumptions disclosed above under “Forward-Looking Statements”, the following assumptions were used to develop these forward-looking financial measures: 2027 Accretion: WSP’s net revenue organic growth of approximately the same level as the average of the last three years for each of the years until 2027 (WSP’s revenue and net revenue were $16,166.8 million and $12,172.2 million, respectively, for the financial year ended December 31, 2024); TRC’s net revenue organic growth in line with the last 4-year compound annual growth rate (“CAGR”) revenue growth (TRC revenue and net revenue were approximately US$1,498.9 million and US$1,192.2 million, respectively for the financial year ended June 30, 2025); TRC Pre-IFRS 16 Adjusted EBITDA margin and Post-IFRS 16 Adjusted EBITDA margin expansion supported by a combination of levers, including utilization and pricing, where significant opportunity has been identified; Expected cost synergies of the Acquisition being fully realized by the end of 2027, with 50% expected to be realized in the first 12 months after closing of the Acquisition. Accretion Upon Closing of the Acquisition: The Acquisition is expected to be immediately accretive upon closing, excluding synergies. WSP’s net revenue organic growth of approximately the same level as the average of the last three years for each of the years until 2027 (WSP’s revenue and net revenue were $16,166.8 million and $12,172.2 million, respectively, for the financial year ended December 31, 2024); TRC’s net revenue organic growth in line with the last 4-year compound annual growth rate (“CAGR”) revenue growth (TRC revenue and net revenue were approximately US$1,498.9 million and US$1,192.2 million, respectively for the financial year ended June 30, 2025); TRC Pre-IFRS 16 Adjusted EBITDA margin and Post-IFRS 16 Adjusted EBITDA margin expansion supported by a combination of levers, including utilization and pricing, where significant opportunity has been identified. TRC Pre-IFRS-16 Adjusted EBITDA and TRC Post-IFRS 16 Adjusted EBITDA: TRC high single digit revenue organic growth for the financial year ending December 31, 2026, in line with TRC’s actual performance for the last four years. TRC Pre-IFRS 16 Adjusted EBITDA margin and Post-IFRS 16 Adjusted EBITDA margin expansion supported by a combination of levers, including utilization and pricing, where significant opportunity has been identified; WSP’s Pro Forma Net Debt to Adjusted EBITDA ratio (upon closing of the Acquisition, and a targeted range within 12 months following closing of the Acquisition): Acquisition closing date assumed to be March 28, 2026; WSP’s Adjusted EBITDA2 for the financial year ending December 31, 2025 ranging from $2.54 billion to $2.56 billion10; TRC’s Post-IFRS 16 Adjusted EBITDA for the financial year ending June 30, 2026 being in line with TRC’s actual performance of the first 3 months of the financial year ending June 30, 2026; All elements of WSP’s consolidated statements of cash flows for the applicable period being in line with those generally experienced by WSP in comparable periods; WSP’s net revenue between $13.8 billion and $14.0 billion for the financial year ending December 31, 2025 (WSP’s net revenue was $12,172.2 million for the financial year ended December 31, 2024, and WSP’s revenue was $16,166.8 million for the financial year ended December 31, 2024); and Cash flow of TRC for the financial year ending June 30, 2026 being in line with TRC Pre-IFRS 16 Adjusted EBITDA for the first 3 months of the financial year ending June 30, 2026. NON-IFRS AND OTHER FINANCIAL MEASURES The Corporation reports its financial results in accordance with International Accounting Standard 34 Interim Financial Reporting. WSP uses a number of financial measures when assessing its results and measuring overall performance. Some of these financial measures are not calculated in accordance with International Financial Reporting Standards Accounting Standards (“IFRS”). Regulation 52-112 respecting Non-GAAP and Other Financial Measures Disclosure prescribes disclosure requirements that apply to the following types of measures used by the Corporation: (i) non-IFRS financial measures; (ii) non-IFRS ratios; (iii) total of segments measures; (iv) capital management measures; and (v) supplementary financial measures. In this document, the following non-IFRS and other financial measures may be used by the Corporation: 2027 Accretion; Accretion Upon Closing of the Acquisition; Net Revenues; Net Revenue Organic Growth, Adjusted EBITDA; Adjusted Net Earnings; Adjusted Net Earnings Per hare; and Net Debt to Adjusted EBITDA ratio. Other than in respect of 2027 Accretion and Accretion Upon Closing of the Acquisition which are each defined below, explanations of the composition and usefulness of these measures can be found in section 19, “Glossary of segment reporting measures, non-IFRS and other financial measures” of WSP’s MD&A for the third quarter and nine-month period ended September 27, 2025 (the “Q3 2025 MD&A”), which section is incorporated by reference in this document, as posted on WSP’s website at www.wsp.com, and filed on SEDAR+ at www.sedarplus.ca. Reconciliations of such measures to the most directly comparable measure under IFRS are provided in section 8, “Financial Review” and section 9, “Liquidity” in each of WSP’s MD&A for the second quarter and six-month period ended June 29, 2024, WSP’s MD&A for the third quarter and nine-month period ended September 28, 2024, WSP’s MD&A for the fourth quarter and year ended December 31, 2024 (the “2024 MD&A”), WSP’s MD&A for the second quarter and six-month period ended June 28, 2025 and in the Q3 2025 MD&A, which sections are also incorporated by reference in this document, as posted on WSP’s website at www.wsp.com, and filed on SEDAR+ at www.sedarplus.ca. The information in this document also includes non-U.S. GAAP financial measures and non-U.S. GAAP financial ratios with respect to TRC, namely TRC Net Revenues, TRC Pre-IFRS 16 Adjusted EBITDA, TRC Post-IFRS 16 Adjusted EBITDA, TRC Pre-IFRS 16 Adjusted EBITDA margin and TRC Post-IFRS 16 Adjusted EBITDA margin. These measures are not recognized measures under U.S. GAAP and do not have standardized meanings prescribed by U.S. GAAP and therefore may not be comparable to similar measures presented by other companies, including WSP’s. Rather, these measures are provided as additional information to complement U.S. GAAP measures by providing further understanding of TRC’s results of operations. Accordingly, these measures should not be considered in isolation nor as a substitute for analysis of TRC’s financial statements reported under U.S. GAAP. WSP discloses TRC Pre-IFRS 16 Adjusted EBITDA because this non-U.S. GAAP measure is a key measure used by TRC to evaluate its business, measure its operating performance and make strategic decisions. WSP believes TRC Pre-IFRS 16 Adjusted EBITDA is useful for investors and others in understanding and evaluating its operations results in the same manner as TRC. However, TRC Pre-IFRS 16 Adjusted EBITDA is not a financial measure calculated in accordance with U.S. GAAP and should not be considered as a substitute for net income, income before income taxes, or any other operating performance measure calculated in accordance with U.S. GAAP. Using this non-U.S. GAAP financial measure to analyze TRC’s business would have material limitations because the calculations are based on the subjective determination of Management regarding the nature and classification of events and circumstances that investors may find significant. In addition, although other companies in its industry may report measures titled adjusted EBITDA or similar measures, such non-U.S. GAAP financial measures may be calculated differently from how TRC calculates non-U.S. GAAP financial measures, which reduces their overall usefulness as comparative measures. Because of these limitations, you should consider these non-U.S. GAAP financial measures alongside other financial performance measures, including net income and TRC’s other financial results presented in accordance with U.S. GAAP. These measures are defined as follows: “TRC Net Revenues” has the same definition as WSP’s definition of “net revenues,” being revenues less direct costs for subconsultants and other direct expenses that are recoverable directly from clients. “TRC Pre-IFRS 16 Adjusted EBITDA” is defined as TRC earnings before net interest and income taxes, excluding depreciation, amortization and acquisition and integration expenses and unusual items. “TRC Post-IFRS 16 Adjusted EBITDA” is defined as the TRC Pre-IFRS 16 Adjusted EBITDA adjusted for operating lease costs. “TRC Pre-IFRS 16 Adjusted EBITDA margin” is defined as the TRC Pre-IFRS 16 Adjusted EBITDA, divided by TRC Net Revenues. “TRC Post-IFRS 16 Adjusted EBITDA margin” is defined as the TRC Post-IFRS 16 Adjusted EBITDA, divided by TRC Net Revenues. WSP uses the following non-IFRS and other financial measures in this document with respect to the Corporation, in each case on a pro-forma basis after giving effect to the Acquisition, the Offering, the Concurrent Private Placement, advances and funds expected to be drawn under the Committed Acquisition Financing and any Acquisition related adjustments, as if each had been completed at the beginning of the relevant period: “WSP Pro Forma Adjusted EBITDA,” for the purpose of calculating the WSP Pro Forma Net Debt to Adjusted EBITDA ratio; “WSP Pro Forma Net Debt to Adjusted EBITDA ratio”; and “WSP Pro Forma Net Revenues”. “2027 Accretion” or “accretive” is calculated as the increase in WSP’s forecasted pro forma adjusted net earnings per share for the financial year ending December 31, 2027 after giving effect to the Acquisition, the Offering, the Concurrent Private Placement, advances and funds expected to be drawn under the Committed Acquisition Financing and any Acquisition-related adjustments, as if it had been completed on January 1, 2027, as compared to WSP’s forecasted adjusted net earnings per share for the financial year ending December 31, 2027 on a stand-alone basis. Refer to “Additional Underlying Assumptions” in this document. “Accretion Upon Closing of the Acquisition” is calculated as the increase in WSP’s forecasted pro forma adjusted net earnings per share immediately after giving effect to the Acquisition, the Offering, the Concurrent Private Placement, advances and funds expected to be drawn under the Committed Acquisition Financing and any Acquisition-related adjustments, as compared to WSP’s forecasted adjusted net earnings per share on a stand-alone basis. Refer to “Additional Underlying Assumptions” in this document. A reconciliation of TRC earnings before net interest and income tax to TRC Pre-IFRS 16 Adjusted EBITDA and TRC Post-IFRS 16 Adjusted EBITDA for the financial year ended June 30, 2025, is provided in the table below: Financial year ended June 30,2025 (in million U.S. dollars) Earnings before net interest and income taxes 87.5 Depreciation 13.8 Amortization 73.1 Acquisition and integration expenses and unusual items 17.9 TRC Pre-IFRS 16 Adjusted EBITDA 192.3 Operating lease costs (IFRS 16 Adjustment) 14.9 TRC Post-IFRS 16 Adjusted EBITDA11 207.2 A reconciliation of TRC Revenues to TRC Net Revenues for the financial year ended June 30, 2025, is provided in the table below: Financial year ended June 30,2025 (in million U.S. dollars) Revenues 1,498.9 Subconsultants and direct costs (306.7) TRC Net Revenues12 1,192.2 A reconciliation of WSP’s Pro Forma Net Revenues for the trailing twelve months ended September 27, 2025 for WSP and financial year ended June 30, 2025 for TRC, is provided in the table below: Trailing Twelve months ended September 27, 2025 (in million U.S. dollars) WSP Net revenues* 13,680.4 TRC Net Revenues (for the financial year ended June 30, 2025 and converted into Canadian dollars) 1,663.4 WSP Pro Forma Net Revenues 15,343.8 * Total of segments measure A reconciliation of WSP’s Pro Forma Adjusted EBITDA for the trailing twelve months ended June 28, 2025 for WSP and financial year ended June 30, 2025 for TRC, is provided in the table below: Trailing Twelve months ended September 27, 2025 (in million U.S. dollars) WSP Adjusted EBITDA 2,501.4 TRC Post-IFRS 16 Adjusted EBITDA (for the financial year ended June 30, 2025 and converted into Canadian dollars) 289.2 WSP Pro Forma Adjusted EBITDA 2,790.6 A reconciliation of WSP’s Pro Forma Net Revenues for the trailing twelve months ended June 28, 2025 for WSP and financial year ended June 30, 2025 for TRC, is provided in the table below: Trailing Twelve months ended June 28, 2025 (in million U.S. dollars) WSP Net revenues* 13,214.2 TRC Net revenues (for the financial year ended June 30, 2025 and converted into Canadian dollars) 1,663.4 WSP Pro Forma Net Revenues 14,877.6 * *Total of segments measure A reconciliation of WSP’s Pro Forma Adjusted EBITDA for the trailing twelve months ended June 28, 2025 for WSP and financial year ended June 30, 2025 for TRC, is provided in the table below: Trailing Twelve months ended June 28, 2025 (in million U.S. dollars) WSP Adjusted EBITDA 2,386.4 TRC Post-IFRS 16 Adjusted EBITDA (for the financial year ended June 30, 2025 and converted into Canadian dollars) 289.2 WSP Pro Forma Adjusted EBITDA 2,675.6 The non-IFRS and other financial measures used in this document do not have a standardized meaning as prescribed by IFRS. Management of the Corporation believes that these non-IFRS and other financial measures provide useful information to investors regarding the financial condition and results of operations of the Corporation and the other entities referenced herein as they provide additional key metrics of their performance. Refer to section 19 “Glossary of segment reporting, non-IFRS and other financial measures” of the Q3 2025 MD&A for more information on the usefulness to investors of each such measures. These non-IFRS and other financial measures are not recognized under IFRS, do not have any standardized meanings prescribed under IFRS and may differ from similar computations as reported by other issuers, and accordingly may not be comparable. These measures should not be viewed as a substitute for the related financial information prepared in accordance with IFRS. PRESENTATION OF FINANCIAL INFORMATION Unless otherwise indicated, all references to “$” in this document are to Canadian dollars and all references to “US$” refer to United States dollars. Where financial information of TRC has been converted from U.S. dollars to Canadian dollars for purposes of comparison to and combination with, financial information of WSP, U.S. dollars have been converted to Canadian dollars at an exchange rate of $1.3952 Canadian dollars per US$1.00. TRC’s financial statements were prepared in accordance with U.S. generally accepted accounting principles (“U.S. GAAP”). IFRS differs in certain material respects from U.S. GAAP. The financial information of TRC presented in this document has not been adjusted to give effect to the differences between U.S. GAAP and IFRS or to accounting policies that comply with IFRS and as applied by WSP, nor has such financial information been conformed from accounting principles under U.S. GAAP to IFRS as issued by the IASB, and thus may not be directly comparable to WSP’s financial information prepared in accordance with IFRS. We have assessed the differences between U.S. GAAP and IFRS for TRC and have determined the impact to be immaterial except for Lease Accounting. Under IFRS, Lease Accounting is governed by IFRS 16 while under U.S. GAAP, it is governed by Accounting Standard Codification (ASC) 842. While similar with regards to the recognition of leases on the balance sheet, the standards have many differences in application. However, the impact of the differences between U.S. GAAP and IFRS for Lease Accounting on the pro forma financial measures presented in this document, namely WSP Pro Forma Net Revenue and WSP Pro Forma Adjusted EBITDA, is immaterial, such that no adjustments would be necessary. WSP’s financial information for the trailing 12-month period ended June 28, 2025 presented herein has been derived by adding WSP’s unaudited interim consolidated financial information for the six-month period ended June 28, 2025 to its audited consolidated financial information for the financial year ended December 31, 2024, and subtracting its unaudited interim consolidated financial information for the six-month period ended June 29, 2024. WSP’s financial information for the trailing 12-month period ended September 27, 2025, presented herein has been derived by adding WSP’s unaudited interim consolidated financial information for the nine-month period ended September 27, 2025 to its audited consolidated financial information for financial year ended December 31, 2024, and subtracting its unaudited interim consolidated financial information for the nine-month period ended September 28, 2024. NO OFFER OR SOLICITATION No securities regulatory authority has either approved or disapproved the contents of this press release. For more information, please contact: Alain Michaud Chief Financial Officer WSP Global Inc. alain.michaud@wsp.com (438) 843-731 1 Based on Engineering News-Record’s (ENR) Top 20 U.S. Design Firms by Sector (Power) list in August 2025, calculated on U.S. domestic revenues (U.S. Revenues) and adjusted to reflect annualization of POWER Engineers, Incorporated’s contribution for the financial year ended December 31, 2024, the assumed completion of the Acquisition as well as WSP U.S. Pro Forma Revenues. The approximate number of employees is as at December 2, 2025. 2 Non-IFRS financial measure or non-IFRS financial ratio that is forward-looking, without a standardized definition under IFRS, which may not be comparable to similar measures or ratios used by other issuers. Please refer to the “Non-IFRS and Other Financial Measures” and “Forward-Looking Statements” disclaimers below. For the financial year ended December 31, 2024, WSP’s adjusted EBITDA was $2,185.7 million, basic net earnings per share attributable to shareholders was $5.40 and adjusted net earnings per share was $8.05. 3 Cost synergies to exceed 3% of TRC’s net revenue are expected to be achieved by the end of 2027, with 50% expected to be realized in the first 12 months after closing of the Acquisition. The cost to realize synergies is estimated at the same level of synergies. 4 Based on ENR’s Top 500 U.S. Design Firms list in August 2025, calculated on U.S. Revenues and adjusted to reflect annualization of POWER Engineers’ contribution for the financial year ended December 31, 2024, the assumed completion of the Acquisition as well as WSP U.S. Pro Forma Revenues. Please refer to the “Forward-Looking Statements” disclaimer below. 5 Based on WSP U.S.’s Power and Energy net revenues for the trailing twelve-month (TTM) period ended June 28, 2025, and TRC’s Power and Energy net revenues for the financial year ended June 30, 2025. USD/CAD exchange rate used to convert TRC net revenue Power and Energy sector into Canadian dollars is 1.3952. Please refer to the “Non-IFRS and Other Financial Measures” and “Forward-Looking Statements” disclaimers below. 6 Pro forma Net Revenues are for the trailing twelve-month period ended June 28, 2025 for WSP, adjusted to reflect annualization of POWER Engineers’ contribution for the financial year ended December 31, 2024 and the assumed completion of the Acquisition. Please refer to the “Forward-Looking Statements” disclaimer below. 7 Non-IFRS financial measure or non-IFRS ratio that is forward-looking, without a standardized definition under IFRS, which may not be comparable to similar measures or ratios used by other issuers. Please refer to the “Non-IFRS and Other Financial Measures” and “Forward-Looking Statements” disclaimers below. 8 Cost synergies to exceed 3% of TRC’s net revenue for the financial year ended June 30, 2025 are expected to be achieved by the end of 2027, with 50% expected to be realized in the first 12 months after closing of the Acquisition. The cost to realize synergies is estimated at the same level of synergies. 9 The Corporation’s assessment of potential synergy opportunities for the Acquisition is primarily based on the information received as part of its due diligence investigation of TRC, its own outside-in perspectives, previous acquisition experience and publicly available information. 10 The target ranges were prepared assuming no fluctuations in foreign exchange rates in markets in which the Corporation operates. The Corporation anticipates organic growth in net revenues by segment will be in the mid-to-high single digits in its Canadian operations, mid single digit growth for its Americas operations, mid-single digits growth in EMEIA and low-to-mid single digit organic contraction in APAC. Head office corporate costs in 2025 are expected to be between $145 million and $160 million. 11 TRC pre-IFRS 16 Adjusted EBITDA and TRC Post-IFRS 16 Adjusted EBITDA for the financial year ended June 30, 2025 are not including the pro forma annualized contribution of acquisitions completed during the 2025 exercise. If we include the annualized contribution of these acquisitions, the pro forma TRC Pre-IFRS 16 Adjusted EBITDA and TRC Post-IFRS 16 Adjusted EBITDA would have been $US196.8M and $US211.7M, respectively. 12 TRC net revenues for the financial year ended June 30, 2025 are not including the proforma annualized contribution of acquisitions completed during the June 30, 2025 financial year-end. If we include the annualized contribution of these acquisitions, the pro forma TRC net revenues would have been $US 1,206.8M.

NFPA Establishes Consolidated Standard for Combustible Dust
January 23, 2025
NFPA 660 will make it easier for all industries to manage dust related hazards making for safer work environments.

General Permit (GP) for CII Stormwater Discharges Proposed for the Charles, Mystic and Neponset River Watersheds
January 8, 2025
On November 1, 2024, FERC Commissioners led a technical conference regarding co-locating large loads at generating facilities.

Ozone Nonattainment Areas in Midwest Reclassified to Serious
January 3, 2025
On Tuesday, December 17th, the United States Environmental Protection Agency (USEPA) issued a final rule reclassifying several ozone nonattainment areas as “Serious” nonattainment for the 2015 ozone national ambient air quality standard.

Deadline Imminent for New Texas Annual Permit Reporting Requirements
December 19, 2024
In 2023, the Texas State Legislature approved Senate Bill 1397 and House Bill 1505, which require that “A person who holds a temporary permit or permit with an indefinite term shall report to the commission annually whether the activity subject to the permit is ongoing” and that the person “shall first report to the Texas Commission on Environmental Quality the status of the permitted activity not later than December 31, 2024”. The Texas Water Code has been amended to include this requirement in Sec. 5.587.

FERC Reviews Large Load Integration at Technical Conference
December 6, 2024
On November 1, 2024, FERC Commissioners led a technical conference regarding co-locating large loads at generating facilities.

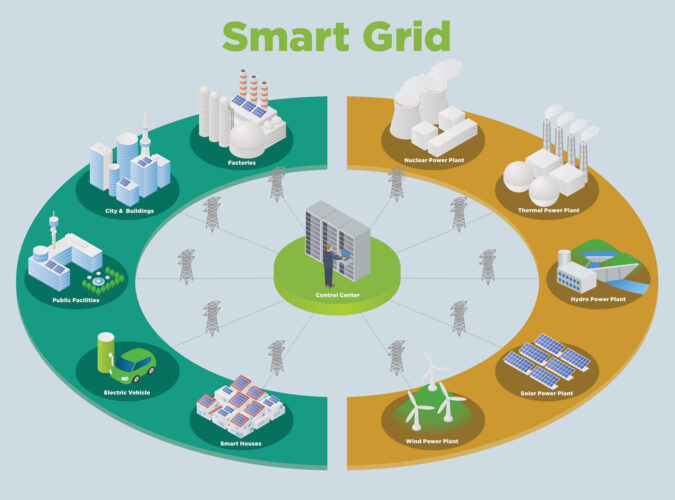
What Is Grid Modernization?
December 2, 2024
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

FERC Issues Guidance to Improve Power System Security and CIP Compliance
September 30, 2024
This update provides details from FERC 2024 staff report from CIP audits, so utilities can improve compliance and reduce security risks.

TRC Acquires Garanzuay Consulting, Amplifying TRC’s Energy Transition Consulting Services in Europe
September 26, 2024
Garanzuay Consulting provides a foundation in Ireland to continue TRC’s growth and expansion in Europe in support of the energy transition for all energy market participants.

NERC Releases 2024 State of Reliability Report
September 19, 2024
The North American Electric Reliability Corporation (NERC) recently released its 2024 State of Reliability report, examining power system performance in calendar year 2023.

Facility Ratings Compliance Through a Corporate Community Approach
August 30, 2024
Facility Ratings play a critical role in the reliable planning and operation of the Bulk Electric System (BES) and yet maintaining compliance with relevant NERC standards remains an industry challenge.

Extreme Geomagnetic Disturbances Impact NERC Planning
August 8, 2024
Learn about the recent geomagnetic disturbance which caused stakeholders within the bulk power system to react swiftly to protect grid reliability. Find out the impacts and what NERC and the industry are doing about it.

Joint Use: Best Practices for Project Success
July 15, 2024
Joint use has never been as important as it is today. With demand for telecommunications infrastructure skyrocketing, governments are investing big in initiatives like the $42.5 billion Broadband Equity Access Deployment Program (BEAD) and the $20.4 billion Rural Digital Opportunity Fund (RDOF).

Consistent NERC Compliance Evidence for Successful Audit Outcomes
June 27, 2024
While utilities often work in technical silos, NERC auditors are trained to cross check compliance evidence and data between interrelated standards.

New NERC Standards Help Protect Against Cyber Attacks
May 23, 2024
As part of NERC’s ongoing effort to bolster Critical Infrastructure Protection (CIP) requirements and enable the implementation of a security improvement concept known as virtualization.

Five Generational Challenges Facing the Utility Workforce
May 10, 2024
In the actively changing energy landscape, utilities are grappling with many workforce-related challenges linked to the ongoing shift towards cleaner energy and the modernization of power grids. As veteran employees retire, it is critical to bridge the knowledge and skill gap by recruiting and developing younger talent.

NERC Compliance Success Through a Corporate Community Approach
May 6, 2024
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

NERC Proposes Changes to Registration Criteria for Inverter Based Resources (IBRs)
April 19, 2024
NERC has submitted for FERC approval new compliance criteria for the registration of IBRs as part of continuing efforts to address reliability risks. It is critical for renewable energy developers, generation owners and transmission owners to understand the potential implications for interconnection studies and interconnection queues.

Shifting to the Cloud: Debunking the Myths of Migrating Utility Data Off Premises
April 14, 2024
This blog delves into common misconceptions surrounding cloud migration in the utility industry, addressing concerns about security, reliability, regulatory compliance, cost effectiveness, and complexity, while highlighting the substantial benefits and strategies for successful adoption.

NERC Proposes Clarifications to EOP Cold Weather Standards
March 26, 2024
NERC has submitted proposed revisions to the EOP-012-2 – Extreme Cold Weather Preparedness and Operations standard, for FERC approval on an expedited basis. The proposed revisions address the remaining key recommendations from the FERC–NERC Joint Inquiry Report into Winter Storm Uri and directives arising from a 2023 FERC Order regarding the previously submitted cold weather standards.

Update to FAC-003-5 Brings Sweeping Changes to Transmission Classifications Starting April 1
March 19, 2024
Update to FAC-003-5 Brings Sweeping Changes to Transmission Classifications Starting April 1

Prevent NERC Compliance Failures with Readiness Reviews
February 20, 2024
Every NERC-registered utility must strive for continuous compliance with their portfolio of applicable NERC Reliability Standards

NERC Releases 2024-2026 Standards Development Plan
January 26, 2024
NERC has submitted its 2024-2026 Reliability Standards Development Plan to the Federal Energy Regulatory Commission (FERC), outlining its current priorities and future standard development plans to protect the reliability of the Bulk Power System over the next three years.

FERC Order 901 Calls for Standards to Address IBR Reliability Gaps
November 27, 2023
Inverter Based Resources are playing central role when it comes to adding new electric generation capacity into the bulk power system.
Locana Awarded Modern Network Management at Esri Infrastructure Management and GIS Conference
November 22, 2023
Locana, an international leader in spatial technology, received the Modern Network Management Award at the 2023 Esri Infrastructure Management and GIS (IMGIS) Conference held in Palm Springs, California, October 10-12, 2023.

Esri Awards Locana with the ArcGIS Cloud Services Specialty Designation
October 4, 2023
Locana, an international leader in spatial technology, received Esri’s ArcGIS Cloud Services Specialty, which designates Locana as an expert in deploying and managing ArcGIS in cloud environments such as Amazon Web Services (AWS) and Microsoft Azure.

The Digital Transformation of the Utility Operations Model: Essential Telecom Network Upgrades to Make Now
October 4, 2023
As technology advances and cybersecurity threats loom, companies must prioritize communications retrofits and upgrades to ensure reliability, availability and business continuity.

FERC Hosts Technical Conference on the Effectiveness and Improvements to CIP-014-3
August 30, 2023
Expert Discussions and Key Takeaways Focus on Physical Security

Offshore Wind: A Critical Energy Solution on the Path to Grid Resiliency and Decarbonization
August 29, 2023
As the urgency to decarbonize and build resiliency grows, renewable energy continues to be a pivotal solution for reshaping the future of power in the U.S. From solar to wind, hydro, geothermal and biomass, each renewable resource has its sweet spot for efficient development, deployment and optimal performance. And while they all have their own pros and cons, it is imperative that we leverage them all into the energy mix to achieve decarbonization goals and ensure adequate capacity to meet increasing load demands.

Intro to NERC Regulatory Guidance on Inverter-Based Resources
August 29, 2023
As renewable energy proliferates across the US power system, the North American Electric Reliability Corporation (NERC) continues to actively address reliability risks resulting from the implementation of inverter-based resources (solar and wind generation technology) connected at both transmission and Distributed Energy Resources (DER) levels.

Strengthening the Future Utility Workforce through Immersive Learning Technology
August 7, 2023
Leveraging new tools and technologies such as mixed and virtual reality (MR/VR) to develop a new generation of skilled engineers and technicians to maintain the reliability and resiliency of the future grid.

FERC Extreme Weather Initiative Will Change the Transmission Planning Process
July 26, 2023
FERC issued a Final Rule directing NERC to develop a new or modified reliability standard addressing transmission system planning performance requirements for extreme heat or cold weather events.

Unleashing the Power of a Human Performance Mindset to Ensure the Next Generation Utility Workforce
June 27, 2023
The impact of adapting behavioral and cultural norms to focus on the principles of human performance cannot be underestimated in building the power workforce of the future.

Advanced Metering Infrastructure (AMI) – How Smart Should A Smart Meter Be?
June 26, 2023
According to the Edison Foundation’s Institute for Electric Innovation, over 124 million smart meters were expected to be installed in 78 percent of US households by the end of 2022.

EPA Issues Clarification of Free Product Removal Requirements
June 20, 2023
EPA recently clarified requirements for LNAPL recovery and remediation.

Modernize Your Field Services with GIS and Work Order Management Combined
June 15, 2023
The role of field service management continues to dominate the world economy, as the market grows at an exponential rate. The market was estimated at 3.2 billion in 2021 and is projected to reach 5.7 billion by the end of 2026.

NERC Files Report on Effectiveness on CIP-014 Physical Security Standard
May 25, 2023
On behalf of the North American Electric Reliability Corporation (NERC), its President and CEO Jim Robb, recently presented to the Federal Energy Regulatory Commission (FERC) a summary of NERC’s report on the effectiveness of NERC’s CIP-014 Physical Security Standard. There were almost 1,700 physical security incidents reported to the Electricity-Information Security Analysis Center (E-ISAC) in 2022, an increase of 10.5% from 2021.

Modeling Power System Hosting Capacity
March 31, 2023
As renewable energy development booms, and distributed energy resources (DERs) proliferate across the grid, the demand for a more efficient and timely interconnection process is at an all-time high. To meet regulatory deadlines and satisfy the needs of both developers and customers, utilities must tackle an increasingly complex array of system impact studies, analyses and reports, under ever shrinking timelines.

FERC Orders Internal Network Security Monitoring Rule to be Finalized
March 14, 2023
FERC directed NERC to develop Reliability Standards to implement INSM within trusted CIP environments.

TRC Companies Assisting LS Power Grid Maine with New Transmission Project in Maine
March 2, 2023
TRC Companies announces its role as a consultant in supporting the new transmission project by LS Power Grid Maine.

Insights from the Odessa II Power System Disturbance
February 22, 2023
NERC and TRE release the Odessa II Power System Disturbance Report
Carrots and Sticks for Building Decarbonization: Incentive Programs and Codes & Standards
January 11, 2023
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

New FERC Orders Will Change Regulatory Process for Inverter Based Resources
January 9, 2023
The Federal Energy Regulatory Commission (FERC) recently proposed actions to keep the regulatory process and requirements ahead of reliability risks resulting from the accelerated deployment of Inverter Based Resources (IBR) based solar, wind and battery storage projects.

NERC Releases Facilities Ratings Best Practices Report
December 19, 2022
NERC report on best practices for utilities that have encountered facility ratings program challenges.

NERC Files Comments in the FERC Generator Interconnection Notice of Proposed Rulemaking
November 21, 2022
The rulemaking addresses improvements needed to reliably facilitate the power industry’s transition to renewable and distributed generating resources utilizing inverter-based technologies.

NERC Releases Inverter-Based Resource Strategy Plan
October 25, 2022
The North American Electric Reliability Corporation (NERC) recently released an Inverter-Based Resource (IBR) Strategy, which details the steps needed to successfully integrate IBR facilities into the planning and operation of the power system. The strategy was put in place due to the rapid interconnection of IBR systems, which are extensively used for solar and wind generating facilities, including new battery-based energy storage systems and are one of the most significant drivers of power grid transformation. Because of control system inconsistencies, IBR facilities pose well-documented risks to power system reliability when this strategy’s practices are not adhered to. NERC’s plan calls attention to the need for thoughtful integration of IBRs and identifies current and future work required to mitigate reliability risks resulting from the deployment of this technology.

NERC Releases 2022 State of Reliability Report
September 16, 2022
The North American Electric Reliability Corporation (NERC) recently released its 2022 State of Reliability report, which examines power system performance in calendar year 2021 and evaluates reliability performance trends. The 2022 report identified six key findings regarding power system performance that are summarized as follows:

NERC Proposes Implementation Guidance for PRC-019-2
August 22, 2022
NERC has proposed implementation guidance for PRC-019-2, the standard that verifies coordination of generating unit facility or synchronous condenser voltage regulating controls, limit functions, equipment capabilities and protection system settings.

Revisions to FAC-001 and FAC-002 Submitted for FERC Approval
July 12, 2022
Reliability Standards FAC-001-4 and FAC-002-will resolve uncertainty regarding the meaning of “materially modify” under the currently effective standards.

FERC Order No. 881-A Has Implications for NERC Compliance Programs
June 23, 2022
Updated Order will have significant impact on NERC compliance programs related to both PRC standards and facilities ratings. Utilities should review the Order’s requirements and prepare for changes needed to remain compliant.

Omaha Metropolitan Utilities District Drives Reliable Operations with Locana Lemur Mobile GIS Solution
June 8, 2022
Locana, a global leader in technology consulting and geospatial systems development, today announced the successful deployment of its LemurSM Solution by Omaha Metropolitan Utilities District (M.U.D.).

NERC’s Revised PRC-024-3 Standard for Inverter-Based Generation Effective in October 2022
May 11, 2022
Changes to PRC-024-3 in support of inverter-based generation performance are going into effect in October of this year. Interconnection programs and documentation procedures may need to be updated in order to maintain compliance.

FERC Issues Notice of Inquiry Regarding Dynamic Line Ratings
April 25, 2022
There are significant technical challenges involved in implementing Dynamic Line Ratings in the planning and operation of utility systems. Utilities should be prepared to modify their NERC compliance programs as necessary to address the potential introduction of DLR in their businesses.

Webinar Replay: Substation Automation – Best Practices for IEC 61850 Implementation
March 29, 2022
Modernizing utility equipment, standards and processes pays dividends for improved safety, security and reliability. But transitioning to a new high-tech system model can be challenging.

New NERC Guidance Supports the Implementation of Grid Forming Inverters
March 8, 2022
NERC has issued a new report highlighting the key attributes of various inverter controls to support proper implementation and to protect reliability.

NERC Recommends Approaches for Underfrequency Load Shedding Programs
February 24, 2022
In a recently released reliability guideline, NERC recommends additional approaches for Underfrequency Load Shedding (UFLS) program design to help utilities effectively consider the effects of Distributed Energy Resources (DERs). The guidance was developed to address the accelerated transition of the power system to locally installed, decarbonized resources that depend on inverters. These new technologies introduce operational controls issues into the electric grid. UFLS data gathering and analysis methodologies may require modification to address reliability risks.

NERC and FERC Recommend Protection System Commissioning Improvements
January 18, 2022
Between 18 and 36 percent of reported utility misoperations were attributed to issues that could have been detected through a properly implemented PSC.

FERC & NERC Issue Joint Report on Freeze Reliability Failures
December 15, 2021
The in-depth report outlines twenty-eight recommendations to address freeze reliability failures, including operating practices and recommendations for NERC standards modifications surrounding generator winterization and gas-electric coordination.

NERC Accelerates Additional Cold Weather Standards Changes
November 22, 2021
At its November 2021 meeting, NERC’s Board of Trustees took aggressive action to advance critical cold weather Reliability Standards. Most notably, the group approved the 2022-2024 Reliability Standards Development Plan, which prioritizes standards projects for the coming years including a resolution to include new cold weather operations, preparedness and coordination standards as high priority development projects.

New Potential Compliance Standards Identified at FERC Technical Conference on Reliability
October 18, 2021
With a focus on the reliability impact of extreme weather and the shortcomings of current system planning approaches, both NERC and FERC conference participants opened the door to potential forthcoming compliance standard enhancements or changes.

NERC Issues Odessa Texas Disturbance Report
September 29, 2021
While NERC has analyzed multiple similar events in California, this is the first disturbance involving a widespread reduction of PV resource power output observed in the Texas Interconnection.

Pacific Gas and Electric Selects TRC as Program Implementer for New Construction Residential All-Electric and Mixed Fuel Programs
September 27, 2021
Pacific Gas and Electric Company (PG&E) formally announced TRC as the designated lead Program Implementer for the Statewide New Construction (SWNC) Residential All-Electric and Mixed Fuel Programs following a competitive solicitation process.

TRC Digital Selected by Snohomish County Public Utility District to Implement Siemens EnergyIP® Meter Data Management
September 15, 2021
Snohomish PUD selected TRC to implement, integrate and deliver their meter data management system (MDMS) on the Siemens EnergyIP® platform as a part of the utility’s Connect Up program.

FERC Approves Modifications to NERC’s Cold Weather-Related Standards
September 7, 2021
The Federal Energy Regulatory Commission has approved changes to three mandatory NERC Reliability Standards that aim to better prepare the North American power system to withstand extreme cold weather events.

Electric Reliability Council of Texas Releases 60-Point Plan for Change
August 23, 2021
ERCOT’s recently released “Roadmap to Improving Grid Reliability” presents a plan for change in Texas that includes increasing electric power generation and purchasing significantly more power reserves.

Prepare for Upcoming NERC Compliance Deadlines
August 20, 2021
With 2020 right around the corner, there are many new NERC standards and standards requirements set to go into effect in the areas of Critical Infrastructure Protection and Transmission Operations and Planning.

Oklahoma Gas & Electric Company uses AI to assess and repair distribution pole damage
August 4, 2021
As part of its grid enhancement program, OG&E will leverage collaborative AI-powered image recognition technology that enables engineers to complete distribution pole inspections with greater accuracy and helps to reduce manual review of images.

Reasons for IT/OT Modernization
August 1, 2021
Opposites attract, and information technology (IT) and operational technology (OT) are no exception. At one end of the digital grid sits IT as a business application, while OT exists at the other end of the digital grid as an asset-oriented application. For decades, IT and OT have been operating separately and are often physically isolated.

IT/OT Convergence Best Practices
August 1, 2021
A successful IT/OT convergence strategy involves identifying desired outcomes, managing the fragmentation of OT solutions, and developing common key performance indicators (KPIs) for both IT and OT teams. This approach helps in optimizing resources, driving effective collaboration, and ensuring a smooth transition towards a unified IT/OT environment.

Developments in Texas and Nationally Mandate Extreme Weather Responses to Protect Reliability
July 23, 2021
Two recent actions will change the current system planning, investment needs and operating procedures for electric utilities. New infrastructure investments and more robust compliance programs will be needed.

TRC Acquires Montreal’s Quatric, Expanding Digital Capabilities for Utilities
June 16, 2021
Today, TRC announced the expansion of its digital capabilities with the acquisition of Quatric, a Montreal, QC and Quincy, MA-based firm that provides engineering services and technology solutions to electric and gas utilities.

NERC’s FAC-008 Guidance on Facility Ratings
May 24, 2021
FAC-008 is one of the most data-intensive standards in the NERC regulatory framework. Compliance has been difficult for many utilities. Recently, FERC made public it’s intent to address serious allegations of facility ratings violations, including a lack of rigor by one utility.

What’s Next? Preparing for Utility Network Migration
May 12, 2021
In preparing for Utility Network Migration, taking an intermediate approach will allow you to resolve some key points. Utility Network Migration will run smoother if you build a “sandbox environment” and begin to 1) prioritize features 2) explore licensing options and 3) practice moving data.

5 Persistent Questions About ArcGIS on HANA
April 9, 2021
While ArcGIS on HANA implementation patterns are emerging rapidly, we continue to hear 5 persistent questions about how implementing ArcGIS on HANA would benefit an organization. Let’s walk through these 5 questions, I’ll show you how we help you get started with ArcGIS on HANA. Then you may realize the benefits this solution promises.

NERC Proposes Revisions to CIP-008
March 27, 2021
NERC’s CIP-008 standard aims to mitigate reliability risks resulting from a Cyber Security Incident by specifying incident response requirements. Newly proposed revisions would augment mandatory reporting to include incidents that compromise, or attempt to compromise, a utility’s Electronic Security Perimeter (ESP) or associated Electronic Access Control or Monitoring Systems (EACMS).

Cold Weather Reliability Preparedness and Hardening
March 22, 2021
The latest weather impacts to power reliability have accelerated the need for mandatory regulatory compliance changes.

TRC Companies Inc. Acquires EMI Consulting
January 27, 2021
Today TRC Companies (“TRC”), announces the expansion of its advanced energy capabilities with the acquisition of EMI Consulting (“EMI”), a Seattle based firm that consults on the strategic development of clean energy solutions including energy efficiency, demand management, decarbonization and customer engagement.

FERC Issues Annual Report on Critical Infrastructure Protection (CIP) Reliability Audits
November 17, 2020
In its 2020 Report on CIP Reliability Audits, the Federal Energy Regulatory Commission found that most of the cybersecurity protection processes and procedures adopted by utilities met the mandatory CIP requirements for protecting the Bulk Electric System. However, there are areas for improvement.

TRC Digital partners with Dominion Energy to evolve its distributed energy resource strategy
September 22, 2020
Dominion Energy, one of the nation’s largest producers and transporters of energy, has partnered with TRC Digital to evaluate, implement and integrate technology to further the utility’s distributed energy goals. TRC Digital will facilitate Dominion Energy’s strategy development and technology execution, allowing Dominion Energy and its customers to accelerate the shift to distributed energy resources (DER) and net carbon reduction.

NERC Issues 2020 State of Reliability Report
September 22, 2020
The Report identifies areas of ongoing concern including generation reserve margins and the reliability risk from shifting the resource mix toward renewables.

TRC Digital and Reactive help utilities measure inertia for a more resilient grid
September 21, 2020
Together, TRC and Reactive combine TRC’s industry-leading power engineering expertise with Reactive’s machine learning software to provide utility teams with high-resolution frequency monitoring and automatic event analysis.

NERC Issues Lessons Learned on Misoperations Due to Mixing Relay Technologies
August 13, 2020
On July 10, 2020 NERC released new Lessons Learned guidance to address situations where multiple composite protection systems have misoperated as a result of mixing protective relay technologies at the remote terminals of directional comparison blocking (DCB) schemes. This technical information will help utilities improve the reliability of the Bulk Power System.

NERC Reliability Standard PRC-024-3 Approved: Frequency and Voltage Protection Settings for Generating Resources
July 28, 2020
On July 9, 2020 NERC standard PRC-024-3 was approved, paving the way for improved protection systems in support of keeping generating resources connected during defined frequency and voltage excursions.

Summary of NERC CIP Standards Updates
June 29, 2020
FERC has released a notice of inquiry seeking comments on potential enhancements to NERC’s Critical Infrastructure Protection (CIP) Reliability Standards.

TRC Digital Partners with Treverity to Put Utility Engineers at the Center of Their Data
June 26, 2020
As part of TRC’s LineHub solution, Treverity helps transmission engineers get a holistic view of the grid through powerful digital data visualization and a customer-centric user interface.

Strategic Electrification
February 4, 2020
As we look to spur strategic electrification across the US, it will be up energy providers and solution implementers to continue sharing ideas, insights and lessons learned

NERC Reliability Report Prioritizes Power System Security Risks for Action
January 2, 2020
NERC’s 2019 ERO Reliability Risk Priorities Report identified and prioritized the major risks facing the utility industry with a particular focus on security issues.

TRC Expands Presence in Power Market with Acquisition of Ohio-based IJUS
October 1, 2018
LOWELL, Mass. – TRC, a leading provider of end-to-end engineering, consulting and construction management solutions fueled by innovative technology, announced today it has acquired IJUS, a top power/utility engineering firm based in Gahanna, Ohio. Terms of the deal were not disclosed.

NERC Proposes Compliance Monitoring and Enforcement Plan for 2019
September 26, 2018
This month, NERC released the first draft of its 2019 Compliance Monitoring and Enforcement Plan (CMEP) which identifies power delivery system risks and outlines compliance audit requirements for next year. The risk elements outlined in the plan include significant differences from previous years, as shown in the table below. Each NERC region must consider these risks as they develop their monitoring and audit scopes for utilities. Utilities should be prepared to be audited and implement any necessary compliance initiatives in these areas.

NERC Standard Extends Maintenance Program Obligations to Generators
February 3, 2014
The approval of NERC Standard PRC-005-2 extends protection system maintenance obligations to Generators and crates one comprehensive standard establishing minimum maintenance activities and maximum time intervals for protection systems and load shedding equipment affecting the bulk electric system.

2026 Megatrends Powering the Shift in India’s Utility Landscape
March 16, 2026
India’s power and utility sector is operating in the midst of a defining decade. In 2026, utilities are finding themselves at the intersection of accelerating demand, renewable scale-up, grid constraints, infrastructure modernization and rising expectations around reliability and affordability.

2026 Megatrends Powering the Shift in the Utility Landscape
January 28, 2026
Every so often, an industry reaches an inflection point — one of those rare moments when change doesn’t just accelerate, it fundamentally redefines the path ahead. For the utility industry, 2026 is that moment.

Discover How to Accelerate True Grid Transformation
January 19, 2026
Discover why true grid transformation requires a revolutionary approach that involves long term systems thinking combined with probabilistic scenario planning.

Enable Predictive Asset Maintenance with AI-Powered Solutions for Utilities
January 19, 2026
Enable AI-powered predictive maintenance with TRC’s remote sensing, computer vision and cloud solutions to reduce outages, enhance grid reliability and turn imagery into actionable asset intelligence for utilities.

Transform Utility Field Operations with Lemur Mobile Mapping
October 23, 2025
Discover how Lemur mobile mapping transforms multiple field management use cases for utilities. Download the white paper now.

Discover How to Transform Operations and Customer Engagement with AMI 2.0
October 23, 2025
Discover how AMI 2.0 transforms utility operations and customer engagement with real-time data, advanced analytics and robust grid-edge innovation.

How Utilities Can Reduce Wildfire Risk
August 26, 2025
Facing growing wildfire threats and limited budgets, utilities must adopt integrated, data-driven strategies for risk assessment, grid hardening and community resilience. Discover five key approaches to cost-effective wildfire mitigation and how expert partners can help safeguard infrastructure and communities.
TRC Appoints Casey Werth as Managing Director, North America Sales for Smart Grid Solutions
August 9, 2025
TRC welcomes Casey Werth as Managing Director, North America Sales for Smart Grid Solutions. A former IBM executive, Werth brings deep expertise in AI, automation and cloud strategy to help utilities modernize and accelerate the energy transition.
TRC and Snohomish County PUD, Transforming Utility Operations with Managed Software as a Service for Meter Data Management
July 31, 2025
Snohomish County Public Utility District, a leading public utility in the Puget Sound region of Washington, has partnered with TRC to implement Siemens’ Gridscale X Meter Data Management System (MDMS) as a cloud-based managed service.

The Transformative Benefits of 3D Facility Mapping for Utilities
June 26, 2025
Discover how modern 3D facility mapping empowers utilities to modernize infrastructure, improve asset management, and enable remote workflows with accurate digital twins, delivering cost savings and operational efficiency.
Why Utilities Need a Comprehensive Data Management Strategy
June 17, 2025
Discover why modern utilities need a thorough data management strategy, from cloud adoption to DER integration.

Exceed Compliance Demands and Improve Leak Survey & Management with Mobile Asset Mapping
April 30, 2025
Leak detection and management is one of the most critical functions for utility companies managing gas infrastructure. As regulatory pressure mounts and public expectations shift, utility operators face a new era where legacy leak survey workflows are struggling to keep up

Grid Resiliency: Perspectives Across the Power Grid
April 16, 2025
In today’s changing energy landscape, grid resiliency is a top priority for all power system owners and operators. The ability to absorb disruptions and maintain power is crucial in an increasingly unpredictable world.

NFPA Establishes Consolidated Standard for Combustible Dust
January 23, 2025
NFPA 660 will make it easier for all industries to manage dust related hazards making for safer work environments.

General Permit (GP) for CII Stormwater Discharges Proposed for the Charles, Mystic and Neponset River Watersheds
January 8, 2025
On November 1, 2024, FERC Commissioners led a technical conference regarding co-locating large loads at generating facilities.

Ozone Nonattainment Areas in Midwest Reclassified to Serious
January 3, 2025
On Tuesday, December 17th, the United States Environmental Protection Agency (USEPA) issued a final rule reclassifying several ozone nonattainment areas as “Serious” nonattainment for the 2015 ozone national ambient air quality standard.

Deadline Imminent for New Texas Annual Permit Reporting Requirements
December 19, 2024
In 2023, the Texas State Legislature approved Senate Bill 1397 and House Bill 1505, which require that “A person who holds a temporary permit or permit with an indefinite term shall report to the commission annually whether the activity subject to the permit is ongoing” and that the person “shall first report to the Texas Commission on Environmental Quality the status of the permitted activity not later than December 31, 2024”. The Texas Water Code has been amended to include this requirement in Sec. 5.587.

FERC Reviews Large Load Integration at Technical Conference
December 6, 2024
On November 1, 2024, FERC Commissioners led a technical conference regarding co-locating large loads at generating facilities.

What Is Grid Modernization?
December 2, 2024
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

FERC Addresses Future Reliability Risks at Technical Conference
November 26, 2024
On October 16, 2024, the Federal Energy Regulatory Commission held its annual Commissioner-led Reliability Technical Conference.

FERC Issues Guidance to Improve Power System Security and CIP Compliance
September 30, 2024
This update provides details from FERC 2024 staff report from CIP audits, so utilities can improve compliance and reduce security risks.

TRC Acquires Garanzuay Consulting, Amplifying TRC’s Energy Transition Consulting Services in Europe
September 26, 2024
Garanzuay Consulting provides a foundation in Ireland to continue TRC’s growth and expansion in Europe in support of the energy transition for all energy market participants.

NERC Releases 2024 State of Reliability Report
September 19, 2024
The North American Electric Reliability Corporation (NERC) recently released its 2024 State of Reliability report, examining power system performance in calendar year 2023.

Facility Ratings Compliance Through a Corporate Community Approach
August 30, 2024
Facility Ratings play a critical role in the reliable planning and operation of the Bulk Electric System (BES) and yet maintaining compliance with relevant NERC standards remains an industry challenge.

Extreme Geomagnetic Disturbances Impact NERC Planning
August 8, 2024
Learn about the recent geomagnetic disturbance which caused stakeholders within the bulk power system to react swiftly to protect grid reliability. Find out the impacts and what NERC and the industry are doing about it.

Joint Use: Best Practices for Project Success
July 15, 2024
Joint use has never been as important as it is today. With demand for telecommunications infrastructure skyrocketing, governments are investing big in initiatives like the $42.5 billion Broadband Equity Access Deployment Program (BEAD) and the $20.4 billion Rural Digital Opportunity Fund (RDOF).

Consistent NERC Compliance Evidence for Successful Audit Outcomes
June 27, 2024
While utilities often work in technical silos, NERC auditors are trained to cross check compliance evidence and data between interrelated standards.

New NERC Standards Help Protect Against Cyber Attacks
May 23, 2024
As part of NERC’s ongoing effort to bolster Critical Infrastructure Protection (CIP) requirements and enable the implementation of a security improvement concept known as virtualization.

Five Generational Challenges Facing the Utility Workforce
May 10, 2024
In the actively changing energy landscape, utilities are grappling with many workforce-related challenges linked to the ongoing shift towards cleaner energy and the modernization of power grids. As veteran employees retire, it is critical to bridge the knowledge and skill gap by recruiting and developing younger talent.

NERC Compliance Success Through a Corporate Community Approach
May 6, 2024
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

NERC Proposes Changes to Registration Criteria for Inverter Based Resources (IBRs)
April 19, 2024
NERC has submitted for FERC approval new compliance criteria for the registration of IBRs as part of continuing efforts to address reliability risks. It is critical for renewable energy developers, generation owners and transmission owners to understand the potential implications for interconnection studies and interconnection queues.

Shifting to the Cloud: Debunking the Myths of Migrating Utility Data Off Premises
April 14, 2024
This blog delves into common misconceptions surrounding cloud migration in the utility industry, addressing concerns about security, reliability, regulatory compliance, cost effectiveness, and complexity, while highlighting the substantial benefits and strategies for successful adoption.

NERC Proposes Clarifications to EOP Cold Weather Standards
March 26, 2024
NERC has submitted proposed revisions to the EOP-012-2 – Extreme Cold Weather Preparedness and Operations standard, for FERC approval on an expedited basis. The proposed revisions address the remaining key recommendations from the FERC–NERC Joint Inquiry Report into Winter Storm Uri and directives arising from a 2023 FERC Order regarding the previously submitted cold weather standards.

Update to FAC-003-5 Brings Sweeping Changes to Transmission Classifications Starting April 1
March 19, 2024
Update to FAC-003-5 Brings Sweeping Changes to Transmission Classifications Starting April 1

Prevent NERC Compliance Failures with Readiness Reviews
February 20, 2024
Every NERC-registered utility must strive for continuous compliance with their portfolio of applicable NERC Reliability Standards

NERC Releases 2024-2026 Standards Development Plan
January 26, 2024
NERC has submitted its 2024-2026 Reliability Standards Development Plan to the Federal Energy Regulatory Commission (FERC), outlining its current priorities and future standard development plans to protect the reliability of the Bulk Power System over the next three years.

NERC & FERC Release Winter Storm Elliott Report
January 2, 2024
NERC and FERC have released their final report on Winter Storm Elliott which provides reinforcement for recommendations in prior cold weather-related disturbance event reports. The Report identifies critical reliability performance shortcomings and the reliability related near misses. NERC states that a crisis was “narrowly dodged.” The Report outlines the steps the industry must take to avoid a repeat in the future.

FERC Order 901 Calls for Standards to Address IBR Reliability Gaps
November 27, 2023
Inverter Based Resources are playing central role when it comes to adding new electric generation capacity into the bulk power system.
Locana Awarded Modern Network Management at Esri Infrastructure Management and GIS Conference
November 22, 2023
Locana, an international leader in spatial technology, received the Modern Network Management Award at the 2023 Esri Infrastructure Management and GIS (IMGIS) Conference held in Palm Springs, California, October 10-12, 2023.

NERC Releases Inverter Based Resources Webinar Series
October 19, 2023
As the power delivery system continues to rapidly evolve due to decarbonization policy initiatives, inverter-based resources (IBRs) are playing an ever-more significant role in generation additions to the bulk power system. NERC and other technical organizations have taken numerous actions to support the reliable integration of these resources.

Esri Awards Locana with the ArcGIS Cloud Services Specialty Designation
October 4, 2023
Locana, an international leader in spatial technology, received Esri’s ArcGIS Cloud Services Specialty, which designates Locana as an expert in deploying and managing ArcGIS in cloud environments such as Amazon Web Services (AWS) and Microsoft Azure.

The Digital Transformation of the Utility Operations Model: Essential Telecom Network Upgrades to Make Now
October 4, 2023
As technology advances and cybersecurity threats loom, companies must prioritize communications retrofits and upgrades to ensure reliability, availability and business continuity.

FERC Issues Order 2023 to Resolve Interconnection Process Issues
September 25, 2023
The Federal Energy Regulatory Commission has approved Order 2023 to facilitate and improve the speed and reliability of adding new energy resources to the power system

FERC Hosts Technical Conference on the Effectiveness and Improvements to CIP-014-3
August 30, 2023
Expert Discussions and Key Takeaways Focus on Physical Security

Offshore Wind: A Critical Energy Solution on the Path to Grid Resiliency and Decarbonization
August 29, 2023
As the urgency to decarbonize and build resiliency grows, renewable energy continues to be a pivotal solution for reshaping the future of power in the U.S. From solar to wind, hydro, geothermal and biomass, each renewable resource has its sweet spot for efficient development, deployment and optimal performance. And while they all have their own pros and cons, it is imperative that we leverage them all into the energy mix to achieve decarbonization goals and ensure adequate capacity to meet increasing load demands.

Intro to NERC Regulatory Guidance on Inverter-Based Resources
August 29, 2023
As renewable energy proliferates across the US power system, the North American Electric Reliability Corporation (NERC) continues to actively address reliability risks resulting from the implementation of inverter-based resources (solar and wind generation technology) connected at both transmission and Distributed Energy Resources (DER) levels.

U.S. EPA’s EJScreen Evolves as the Agency Advances Environmental Justice
August 21, 2023
EJScreen is currently at the forefront of federal efforts to identify potential disproportionate environmental burdens and communities with potential environmental justice (EJ) concerns.

Strengthening the Future Utility Workforce through Immersive Learning Technology
August 7, 2023
Leveraging new tools and technologies such as mixed and virtual reality (MR/VR) to develop a new generation of skilled engineers and technicians to maintain the reliability and resiliency of the future grid.

FERC Extreme Weather Initiative Will Change the Transmission Planning Process
July 26, 2023
FERC issued a Final Rule directing NERC to develop a new or modified reliability standard addressing transmission system planning performance requirements for extreme heat or cold weather events.

Unleashing the Power of a Human Performance Mindset to Ensure the Next Generation Utility Workforce
June 27, 2023
The impact of adapting behavioral and cultural norms to focus on the principles of human performance cannot be underestimated in building the power workforce of the future.

Advanced Metering Infrastructure (AMI) – How Smart Should A Smart Meter Be?
June 26, 2023
According to the Edison Foundation’s Institute for Electric Innovation, over 124 million smart meters were expected to be installed in 78 percent of US households by the end of 2022.

FERC Approves Plan to Register Certain Inverter-Based Resources as part of NERC Mandatory Standards Compliance Program
June 21, 2023
FERC issued an order approving NERC’s compliance filings.

Modernize Your Field Services with GIS and Work Order Management Combined
June 15, 2023
The role of field service management continues to dominate the world economy, as the market grows at an exponential rate. The market was estimated at 3.2 billion in 2021 and is projected to reach 5.7 billion by the end of 2026.

Advancing Telecommunication Projects: A Guide for High Level Design
June 6, 2023
TRC has developed utility network Master Plans and designed and architected utility-wide networks

NERC Files Report on Effectiveness on CIP-014 Physical Security Standard
May 25, 2023
On behalf of the North American Electric Reliability Corporation (NERC), its President and CEO Jim Robb, recently presented to the Federal Energy Regulatory Commission (FERC) a summary of NERC’s report on the effectiveness of NERC’s CIP-014 Physical Security Standard. There were almost 1,700 physical security incidents reported to the Electricity-Information Security Analysis Center (E-ISAC) in 2022, an increase of 10.5% from 2021.

FERC Issues Order on Cold Weather Reliability Standards
April 27, 2023
FERC has approved two NERC proposed cold weather-related reliability standards.

Modeling Power System Hosting Capacity
March 31, 2023
As renewable energy development booms, and distributed energy resources (DERs) proliferate across the grid, the demand for a more efficient and timely interconnection process is at an all-time high. To meet regulatory deadlines and satisfy the needs of both developers and customers, utilities must tackle an increasingly complex array of system impact studies, analyses and reports, under ever shrinking timelines.

FERC Orders Internal Network Security Monitoring Rule to be Finalized
March 14, 2023
FERC directed NERC to develop Reliability Standards to implement INSM within trusted CIP environments.

TRC Companies Assisting LS Power Grid Maine with New Transmission Project in Maine
March 2, 2023
TRC Companies announces its role as a consultant in supporting the new transmission project by LS Power Grid Maine.

Insights from the Odessa II Power System Disturbance
February 22, 2023
NERC and TRE release the Odessa II Power System Disturbance Report
Carrots and Sticks for Building Decarbonization: Incentive Programs and Codes & Standards
January 11, 2023
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

New FERC Orders Will Change Regulatory Process for Inverter Based Resources
January 9, 2023
The Federal Energy Regulatory Commission (FERC) recently proposed actions to keep the regulatory process and requirements ahead of reliability risks resulting from the accelerated deployment of Inverter Based Resources (IBR) based solar, wind and battery storage projects.

NERC Releases Facilities Ratings Best Practices Report
December 19, 2022
NERC report on best practices for utilities that have encountered facility ratings program challenges.

NERC Files Comments in the FERC Generator Interconnection Notice of Proposed Rulemaking
November 21, 2022
The rulemaking addresses improvements needed to reliably facilitate the power industry’s transition to renewable and distributed generating resources utilizing inverter-based technologies.

NERC Releases Inverter-Based Resource Strategy Plan
October 25, 2022
The North American Electric Reliability Corporation (NERC) recently released an Inverter-Based Resource (IBR) Strategy, which details the steps needed to successfully integrate IBR facilities into the planning and operation of the power system. The strategy was put in place due to the rapid interconnection of IBR systems, which are extensively used for solar and wind generating facilities, including new battery-based energy storage systems and are one of the most significant drivers of power grid transformation. Because of control system inconsistencies, IBR facilities pose well-documented risks to power system reliability when this strategy’s practices are not adhered to. NERC’s plan calls attention to the need for thoughtful integration of IBRs and identifies current and future work required to mitigate reliability risks resulting from the deployment of this technology.

NERC Releases 2022 State of Reliability Report
September 16, 2022
The North American Electric Reliability Corporation (NERC) recently released its 2022 State of Reliability report, which examines power system performance in calendar year 2021 and evaluates reliability performance trends. The 2022 report identified six key findings regarding power system performance that are summarized as follows:

NERC Proposes Implementation Guidance for PRC-019-2
August 22, 2022
NERC has proposed implementation guidance for PRC-019-2, the standard that verifies coordination of generating unit facility or synchronous condenser voltage regulating controls, limit functions, equipment capabilities and protection system settings.

The Use Case Benefits of GIS Modernization for Utilities
August 10, 2022
Additional Restrictions for Major Modifications Other restrictions will come into play for new Major Sources, those that have a potential to emit 50 tons per year or more of VOC or NOx and “major modifications” that result in a VOC emission increase that exceeds 25 tons per year and also exceeds 25 tons per year when aggregated with all creditable increases and decreases in emissions of VOC from the source over any period of five consecutive years, which includes the calendar year in which the increase will occur. For sources that are major due to NOx emissions, a NOx emission increase that exceeds 25 tons per year and exceeds 25 tons per year when aggregated with creditable increases and decreases over the five-year period is also deemed to be a major modification. If a major modification occurs, the source is required to utilize the Lowest Achievable Emission Rate (or LAER) for the pollutant(s) that exceed 25 tons per year aggregated over the five-year period. However, Best Available Control Technology (BACT) can be substituted for LAER under certain conditions. Additionally, emissions must be offset as a means to advancing the area toward attaining the ozone standard. These same requirements will apply to newly constructed Major Sources. Upcoming Deadlines With these actions, the impacted areas will now have until August 3, 2027, to reach attainment. If they do not, USEPA is again obligated to reclassify ongoing nonattainment status to Severe nonattainment, reducing the Major Source threshold in half to just 25 tons per year. In the meantime, the states will be required to revise State Implementation Plans to demonstrate that attainment will be achieved by this deadline. A unique consideration in Wisconsin affects sources subject to a Registration Operation Permit. These permits establish annual emission limits as a percentage of the Major Source threshold (25, 50, or 80 percent depending on the Permit). For these sources, the annual emission limit for VOC and NOx will automatically be cut in half on January 16, 2025. Sources in the ozone nonattainment areas that hold these permits should evaluate whether the Registration Permit provides a long-term option given that the annual emission limits have been cut in half now and may again be cut in half in three years’ time. Next Steps: TRC Can Help TRC is available to support your air compliance and permitting needs by offering expert in-house resources to perform: Ambient Monitor Siting Evaluation Ambient Monitor Deployment, Operation and Maintenance For more information, contact Melanie Klamar, Robert VandenMeiracker and Mike Zebell.

Revisions to FAC-001 and FAC-002 Submitted for FERC Approval
July 12, 2022
Reliability Standards FAC-001-4 and FAC-002-will resolve uncertainty regarding the meaning of “materially modify” under the currently effective standards.

FERC Order No. 881-A Has Implications for NERC Compliance Programs
June 23, 2022
Updated Order will have significant impact on NERC compliance programs related to both PRC standards and facilities ratings. Utilities should review the Order’s requirements and prepare for changes needed to remain compliant.

Brookings Municipal Utilities Streamlines Processes, Boosts Efficiency with Modern GIS
June 14, 2022
Locana, a global leader in technology consulting and geospatial systems development, announced Brookings Municipal Utilities (BMU) successful deployment of a modern geospatial enterprise leveraging Locana services.

Omaha Metropolitan Utilities District Drives Reliable Operations with Locana Lemur Mobile GIS Solution
June 8, 2022
Locana, a global leader in technology consulting and geospatial systems development, today announced the successful deployment of its LemurSM Solution by Omaha Metropolitan Utilities District (M.U.D.).

NERC’s Revised PRC-024-3 Standard for Inverter-Based Generation Effective in October 2022
May 11, 2022
Changes to PRC-024-3 in support of inverter-based generation performance are going into effect in October of this year. Interconnection programs and documentation procedures may need to be updated in order to maintain compliance.

FERC Issues Notice of Inquiry Regarding Dynamic Line Ratings
April 25, 2022
There are significant technical challenges involved in implementing Dynamic Line Ratings in the planning and operation of utility systems. Utilities should be prepared to modify their NERC compliance programs as necessary to address the potential introduction of DLR in their businesses.

Creating a Culture of Safety During Plant Decommissioning
April 13, 2022
Creating intrinsically motivated safety cultures within nuclear power plants is imperative, especially during the decommissioning process. Employees’ long-standing beliefs and attitudes often determine their decisions and actions, so cultivating a safety-first culture requires commitment and accountability.

Start Your Batteries: Mass Fleet Electrification is Coming (And What We Can do to Prepare)
April 13, 2022
As we plan for and make early investments for fleets, we’ll be paving the way for higher degrees of market penetration of passenger vehicles and other modes of transportation as well.

TRC Selected as Systems Integrator for Otter Tail Power Company’s Advanced Metering Infrastructure Program
April 5, 2022
Otter Tail Power Company selects TRC to serve as systems integrator for their AMI program covering northwestern Minnesota, eastern North Dakota, and northeastern South Dakota.

Webinar Replay: Substation Automation – Best Practices for IEC 61850 Implementation
March 29, 2022
Modernizing utility equipment, standards and processes pays dividends for improved safety, security and reliability. But transitioning to a new high-tech system model can be challenging.

New NERC Guidance Supports the Implementation of Grid Forming Inverters
March 8, 2022
NERC has issued a new report highlighting the key attributes of various inverter controls to support proper implementation and to protect reliability.

NERC Recommends Approaches for Underfrequency Load Shedding Programs
February 24, 2022
In a recently released reliability guideline, NERC recommends additional approaches for Underfrequency Load Shedding (UFLS) program design to help utilities effectively consider the effects of Distributed Energy Resources (DERs). The guidance was developed to address the accelerated transition of the power system to locally installed, decarbonized resources that depend on inverters. These new technologies introduce operational controls issues into the electric grid. UFLS data gathering and analysis methodologies may require modification to address reliability risks.

The Best Process for Transforming Thermal Generation Power Plants
February 9, 2022
Faced with an aging fleet, stricter environmental regulations, reduced costs for natural gas and competition from renewables, more than 600 power plants have been decommissioned in the last 20 years, a pace that will increase with the announced closure of nearly 350 additional plants by 2025.

Ensuring a Just Transition: Optimizing Opportunities for All in the Low-Carbon Future
January 24, 2022
Carbon elimination of the magnitude needed to address climate change requires systems-level change that can only be reached by incremental, ground-up progress, building upon what we have achieved thus far.

NERC and FERC Recommend Protection System Commissioning Improvements
January 18, 2022
Between 18 and 36 percent of reported utility misoperations were attributed to issues that could have been detected through a properly implemented PSC.

FERC & NERC Issue Joint Report on Freeze Reliability Failures
December 15, 2021
The in-depth report outlines twenty-eight recommendations to address freeze reliability failures, including operating practices and recommendations for NERC standards modifications surrounding generator winterization and gas-electric coordination.

Decarbonization: A Systems-Level Challenge and Actions to Address Climate Change
December 7, 2021
Carbon elimination of the magnitude needed to address climate change requires systems-level change that can only be reached by incremental, ground-up progress, building upon what we have achieved thus far.

NERC Accelerates Additional Cold Weather Standards Changes
November 22, 2021
At its November 2021 meeting, NERC’s Board of Trustees took aggressive action to advance critical cold weather Reliability Standards. Most notably, the group approved the 2022-2024 Reliability Standards Development Plan, which prioritizes standards projects for the coming years including a resolution to include new cold weather operations, preparedness and coordination standards as high priority development projects.

PRC-002-2 Disturbance Monitoring and Reporting Standard: Initial Mandatory Implementation Plan Dates Approach
November 18, 2021
The Federal Energy Regulatory Commission approved PRC-002-2 in September, 2015. The initial due date for system studies necessary to identify locations for the collection of disturbance related data under Requirement R1 is January 1, 2017.

10 Takeaways from the COP26 Climate Meeting
November 17, 2021
There are compelling reasons to be optimistic about the outcomes of the COP26 meeting. Notably, agreement among all nations that more needs to be done, by both private and governmental bodies, to contain and mitigate climate change.
The Price of Natural Gas: Onward and Upward or Just a Temporary Blip?
November 12, 2021
Most industry experts agree that weather aside, the global energy and gas markets are likely to remain uncertain with supply and market demand becoming tighter and more challenging to forecast.

Six Considerations for a Successful Utility Network Cloud Implementation
October 26, 2021
For any GIS manager or IT professional tasked with implementing ArcGIS Utility Network (UN), knowing where to start can be daunting. If not properly planned, a UN setup in the cloud can be significantly more expensive and less accessible, stable, and secure.

How Do Energy Storage Systems Work?
October 18, 2021
For more than five decades, TRC has brought efficient, resilient energy systems to the world. We understand the challenges of implementing energy storage projects.

New Potential Compliance Standards Identified at FERC Technical Conference on Reliability
October 18, 2021
With a focus on the reliability impact of extreme weather and the shortcomings of current system planning approaches, both NERC and FERC conference participants opened the door to potential forthcoming compliance standard enhancements or changes.

On the Road to Decarbonization: The Role of All-Source Competitive Solicitations
October 14, 2021
All-Source Competitive Solicitations offer utilities an alternative to centralized planning, construction and dispatch of power supplies, helping to usher in a new era of market-driven technology innovation.

How Does a Distribution Grid Work?
October 2, 2021
Electric distribution systems rely on sophisticated technology to provide power when needed. Electricity is generated on-demand, which means there are often peak periods when providers see a greater need for power and the system must prove responsive.

Amplifying the Next Phase of Fleet Electrification: The Pickup
September 30, 2021
TRC’s analysis for one client fleet shows that even a $70,000 EV can compete on cost with a comparable gas-hybrid vehicle priced at $40,000 – at least in California where upfront and ongoing incentives stack up quickly.

NERC Issues Odessa Texas Disturbance Report
September 29, 2021
While NERC has analyzed multiple similar events in California, this is the first disturbance involving a widespread reduction of PV resource power output observed in the Texas Interconnection.

Pacific Gas and Electric Selects TRC as Program Implementer for New Construction Residential All-Electric and Mixed Fuel Programs
September 27, 2021
Pacific Gas and Electric Company (PG&E) formally announced TRC as the designated lead Program Implementer for the Statewide New Construction (SWNC) Residential All-Electric and Mixed Fuel Programs following a competitive solicitation process.

TRC Digital Selected by Snohomish County Public Utility District to Implement Siemens EnergyIP® Meter Data Management
September 15, 2021
Snohomish PUD selected TRC to implement, integrate and deliver their meter data management system (MDMS) on the Siemens EnergyIP® platform as a part of the utility’s Connect Up program.

FERC Approves Modifications to NERC’s Cold Weather-Related Standards
September 7, 2021
The Federal Energy Regulatory Commission has approved changes to three mandatory NERC Reliability Standards that aim to better prepare the North American power system to withstand extreme cold weather events.

NERC’s Generator Relay Loadability Standard is Now in Effect
August 30, 2021
Faced with an aging fleet, stricter environmental regulations, reduced costs for natural gas and competition from renewables, more than 600 power plants have been decommissioned in the last 20 years, a pace that will increase with the announced closure of nearly 350 additional plants by 2025. With a goal of being net-zero carbon by 2050, many power generators are faced with critical decisions regarding their thermal generation plants. Should they continue operation, repower, re-purpose or retire their plants? In the competitive power generation market, coal-fired plants are getting squeezed on multiple fronts including lower prices for renewables (e.g., wind and solar) and gas, inefficient cyclical operation and, in some instances, by state efforts to curtail the use of coal. Foregoing the retail market and partnering with a data center for mining cryptocurrency can represent a winning financial proposition for both parties. Some states are actively encouraging the co-locating of data centers at generation sites, while others are actively working to keep plants operational in order to preserve the jobs at the plants and in the mines. In some regional transmission organizations, such as PJM, newer natural gas fired generation units are favored over older units because of their more efficient turbines and larger size. Older natural gas units are at risk of becoming stranded assets as cheaper renewables come online and the industry commitments to net zero emissions. There are reports that banks Citigroup Inc and JP Morgan Chase & Co will strengthen their financing restrictions on thermal gas plants, similar to what they’ve already done for coal projects.

NERC Seeks to Improve GADS Reliability Performance Reporting
August 26, 2021
Faced with an aging fleet, stricter environmental regulations, reduced costs for natural gas and competition from renewables, more than 600 power plants have been decommissioned in the last 20 years, a pace that will increase with the announced closure of nearly 350 additional plants by 2025. With a goal of being net-zero carbon by 2050, many power generators are faced with critical decisions regarding their thermal generation plants. Should they continue operation, repower, re-purpose or retire their plants? In the competitive power generation market, coal-fired plants are getting squeezed on multiple fronts including lower prices for renewables (e.g., wind and solar) and gas, inefficient cyclical operation and, in some instances, by state efforts to curtail the use of coal. Foregoing the retail market and partnering with a data center for mining cryptocurrency can represent a winning financial proposition for both parties. Some states are actively encouraging the co-locating of data centers at generation sites, while others are actively working to keep plants operational in order to preserve the jobs at the plants and in the mines. In some regional transmission organizations, such as PJM, newer natural gas fired generation units are favored over older units because of their more efficient turbines and larger size. Older natural gas units are at risk of becoming stranded assets as cheaper renewables come online and the industry commitments to net zero emissions. There are reports that banks Citigroup Inc and JP Morgan Chase & Co will strengthen their financing restrictions on thermal gas plants, similar to what they’ve already done for coal projects.

Prepare for Upcoming NERC Compliance Deadlines
August 20, 2021
With 2020 right around the corner, there are many new NERC standards and standards requirements set to go into effect in the areas of Critical Infrastructure Protection and Transmission Operations and Planning.

TRC Talks – Attaching Telecommunications Fiber in the Supply Space
August 10, 2021
Today’s utility and communications infrastructure is being challenged to support a growing demand for automation, broadband and 5G network services. Attaching fiber in the power distribution or supply space can mitigate risks related to overloading and overcrowding.

Oklahoma Gas & Electric Company uses AI to assess and repair distribution pole damage
August 4, 2021
As part of its grid enhancement program, OG&E will leverage collaborative AI-powered image recognition technology that enables engineers to complete distribution pole inspections with greater accuracy and helps to reduce manual review of images.

Reasons for IT/OT Modernization
August 1, 2021
Opposites attract, and information technology (IT) and operational technology (OT) are no exception. At one end of the digital grid sits IT as a business application, while OT exists at the other end of the digital grid as an asset-oriented application. For decades, IT and OT have been operating separately and are often physically isolated.

IT/OT Convergence Best Practices
August 1, 2021
A successful IT/OT convergence strategy involves identifying desired outcomes, managing the fragmentation of OT solutions, and developing common key performance indicators (KPIs) for both IT and OT teams. This approach helps in optimizing resources, driving effective collaboration, and ensuring a smooth transition towards a unified IT/OT environment.

NERC’s FAC-008 Guidance on Facility Ratings
May 24, 2021
FAC-008 is one of the most data-intensive standards in the NERC regulatory framework. Compliance has been difficult for many utilities. Recently, FERC made public it’s intent to address serious allegations of facility ratings violations, including a lack of rigor by one utility.

What’s Next? Preparing for Utility Network Migration
May 12, 2021
In preparing for Utility Network Migration, taking an intermediate approach will allow you to resolve some key points. Utility Network Migration will run smoother if you build a “sandbox environment” and begin to 1) prioritize features 2) explore licensing options and 3) practice moving data.

NERC Issues Battery Energy Storage Systems Reliability Guidance
April 22, 2021
While NERC has recently published a reliability guideline addressing inverter-based resources generally, they are now giving more attention to the various potential uses of BESS to support effective implementation with newly released guidance.

5 Persistent Questions About ArcGIS on HANA
April 9, 2021
While ArcGIS on HANA implementation patterns are emerging rapidly, we continue to hear 5 persistent questions about how implementing ArcGIS on HANA would benefit an organization. Let’s walk through these 5 questions, I’ll show you how we help you get started with ArcGIS on HANA. Then you may realize the benefits this solution promises.

NERC Proposes Revisions to CIP-008
March 27, 2021
NERC’s CIP-008 standard aims to mitigate reliability risks resulting from a Cyber Security Incident by specifying incident response requirements. Newly proposed revisions would augment mandatory reporting to include incidents that compromise, or attempt to compromise, a utility’s Electronic Security Perimeter (ESP) or associated Electronic Access Control or Monitoring Systems (EACMS).

NERC Releases 2021 Compliance Monitoring and Enforcement Findings
February 8, 2021
NERC’s 2021 Compliance Monitoring and Enforcement Program reframes the previous year’s risks and their associated areas of focus. Utilities should review their compliance programs and internal controls to determine if enhancement or changes are need to maintain compliance.

NERC Proposes Revision of Pending TPL-001-5.1 Standard
January 20, 2021
NERC has recently undertaken important standards and guidance development activities related to the proliferation of inverter-based technologies such as solar and wind generation, as well as battery energy storage which is growing as an industry solution to ensure the reliability of renewable power for end-use customers.

NERC and FERC Take Action on Facilities Ratings
December 4, 2020
There has been significant work across the electric industry to improve facility ratings related processes, programs, frameworks, internal controls and best practices. Yet this continues to be a challenging area for utilities, particularly from an asset management and regulatory compliance perspective.

FERC Issues Annual Report on Critical Infrastructure Protection (CIP) Reliability Audits
November 17, 2020
In its 2020 Report on CIP Reliability Audits, the Federal Energy Regulatory Commission found that most of the cybersecurity protection processes and procedures adopted by utilities met the mandatory CIP requirements for protecting the Bulk Electric System. However, there are areas for improvement.

NERC Issues 2020 State of Reliability Report
September 22, 2020
The Report identifies areas of ongoing concern including generation reserve margins and the reliability risk from shifting the resource mix toward renewables.

TRC Digital and Reactive help utilities measure inertia for a more resilient grid
September 21, 2020
Together, TRC and Reactive combine TRC’s industry-leading power engineering expertise with Reactive’s machine learning software to provide utility teams with high-resolution frequency monitoring and automatic event analysis.

NERC Reliability Standard PRC-024-3 Approved: Frequency and Voltage Protection Settings for Generating Resources
July 28, 2020
On July 9, 2020 NERC standard PRC-024-3 was approved, paving the way for improved protection systems in support of keeping generating resources connected during defined frequency and voltage excursions.

Summary of NERC CIP Standards Updates
June 29, 2020
FERC has released a notice of inquiry seeking comments on potential enhancements to NERC’s Critical Infrastructure Protection (CIP) Reliability Standards.

TRC Digital Partners with Treverity to Put Utility Engineers at the Center of Their Data
June 26, 2020
As part of TRC’s LineHub solution, Treverity helps transmission engineers get a holistic view of the grid through powerful digital data visualization and a customer-centric user interface.

TRC Digital and Enbala can help utilities monitor, control and optimize distributed energy resources
April 17, 2020
Distributed energy resources (DERs) are changing the way utilities think about power generation and energy flow. TRC and Enbala can offer utilities a multi-layered solution that highlights the strengths of each company.

NERC Protection System Compliance Studies Due This Year
February 24, 2020
NERC’s PRC-027-1 standard was approved by FERC in 2018 and is set to go into effect on October 1, 2020. Utilities should begin preparing now to meet compliance requirements which include significant system studies.

Strategic Electrification
February 4, 2020
As we look to spur strategic electrification across the US, it will be up energy providers and solution implementers to continue sharing ideas, insights and lessons learned

New York State Finalizes Emission Limits for Power Generators
January 21, 2020
On January 16, 2020, the New York State Department of Environmental Conservation (NYSDEC) finalized a rulemaking limiting nitrogen oxide (NOx) emissions from existing simple cycle and regenerative peaking combustion turbines with a nameplate capacity of 15 megawatts (MW) or greater during the ozone season (May 1 – October 31).

NERC Compliance Assurance: Maintaining Cross Functional Data Integrity
January 21, 2020
Assuring continued power system reliability is a complex undertaking for utilities. Balancing the demands of system changes and regulatory compliance is an essential strategy for optimizing ongoing operations. Given the wide range of NERC standard families that require simultaneous data management for compliance, data integrity, data flow and data verification are critical for avoiding violations that can impact electric service to customers and communities.

NERC Reliability Report Prioritizes Power System Security Risks for Action
January 2, 2020
NERC’s 2019 ERO Reliability Risk Priorities Report identified and prioritized the major risks facing the utility industry with a particular focus on security issues.

NERC Reliability Report Prioritizes Power System Risks
November 21, 2019
Looking ahead to the many changes coming to North America’s Bulk Power System (BPS), NERC’s 2019 ERO Reliability Risk Priorities Report highlights the top issues requiring industry and regulatory attention and recommends actions for the ongoing protection of BPS reliability.

NERC Pursues Changes to Protection Relay and Control (PRC) Standards
September 24, 2019
Two Standards Authorization Requests currently being debated in the NERC stakeholder engagement process could help clarify PRC standards obligations for generator owners and operators.

New York State Proposes Emissions Limits for Power Generators
March 22, 2019
On February 27, 2019, the New York State Department of Environmental Conservation (NYSDEC) released a proposed rulemaking limiting nitrogen oxide (NOx) emissions from existing simple cycle and regenerative peaking combustion turbines with a nameplate capacity of 15 megawatts (MW) or greater during the ozone season (May 1 – October 31).

NERC to Modify Standard and Develop Compliance Guidance to Accommodate Inverter-Based Generation Technologies
February 20, 2019
Renewable energy systems have dramatically changed the power generation resource mix. These new generation technologies no longer involve directly coupled rotating generators which were once standard in the industry. Now, inverters that change Direct Current (DC) electricity to the Alternating Current (AC) electricity suitable for delivery via AC transmission systems are becoming more prevalent, raising reliability…

NERC Addresses Single Points of Failure in Protection Systems Among Other FERC Concerns
October 25, 2018
In 2017 Oregon Governor Kate Brown took bold action by directing state agencies to chart a 10-year course towards greater energy efficiency in affordable housing to help remove the energy burden on low-income communities. This initiative took flight under the direction of the Oregon Housing and Community Services, the Oregon Public Utility Commission and the Oregon Department of Energy, which created the newly released Ten-Year Plan: Reducing the Energy Burden in Oregon Affordable Housing. Last summer, OHCS hired TRC to assist in the development of these two deliverables. As the Project Lead, I was given the opportunity to experience first-hand both the excitement and challenges of this initiative. After almost 15 years working on low-income energy efficiency programs, this project allowed me to view this familiar topic through a new lens. Instead of designing a building-level incentive program, I was focused on the low-income population – the actual people living with energy challenges – and evaluating how efficiency could help to reduce their economic, health and housing burdens. One of my first discoveries was an analysis of the energy burden gap of the low-income population in Oregon that showed the difference between a typical low-income household’s actual energy costs and an affordable energy cost (6 percent of the household’s income) is significant – and totaled $345 million statewide in 2017. (Nationwide, that gap is over $47 billion per year.) Despite my surprise at the size of this gap, I still wasn’t prepared for what we found next.

NERC Proposes Compliance Monitoring and Enforcement Plan for 2019
September 26, 2018
This month, NERC released the first draft of its 2019 Compliance Monitoring and Enforcement Plan (CMEP) which identifies power delivery system risks and outlines compliance audit requirements for next year. The risk elements outlined in the plan include significant differences from previous years, as shown in the table below. Each NERC region must consider these risks as they develop their monitoring and audit scopes for utilities. Utilities should be prepared to be audited and implement any necessary compliance initiatives in these areas.

NERC Calls for New Approach to Reliability Planning Due to Gas Supply Disruption Risks
December 14, 2017
A recently published NERC report concludes that as reliance on natural gas to meet electric generation requirements increases, additional planning and operational measures must be considered to mitigate power system reliability risks.

NERC CIP-013-1 Standard for Supply Chain Risk Management
September 29, 2017
NERC has filed mandatory standard CIP-013-1 for supply chain risk management, requiring controls to mitigate cyber threats and their impact to the reliable operation of the Bulk Electric System.

NERC Identifies New Reliability Risk due to Utility Scale Solar Generation Inverter Design
June 13, 2017
NERC has released a report documenting its findings and recommendations related to reliability risks from utility scale solar generation projects with implications for PRC-024 compliance, as well as generation, interconnection and protection system technologies.

TRC and partners win $1 million grant for engineering innovative New York microgrid
April 20, 2017
TRC is proud to support Huntington, NY bolster power reliability and climate-change resiliency with a sophisticated new “community microgrid’’ combining solar energy, a fuel cell, biogas and traditional natural gas to deliver electricity and heat to local customers and institutions.

Looking ahead: a changing energy landscape and strategies for success
February 13, 2017
Amid all the changes in the energy industry in 2017, one of the most interesting and complex is playing out in California and New York as those states begin to re-think how best to value and purchase energy efficiency. As TRC’s Carmen Henrikson and Bob Callender explain in this TRC article, the era of paying…

Successful Interconnection of Utility Scale Solar Projects – Strategies to Stay on Schedule and on Budget
November 2, 2016
Growth in solar power creates challenges for both project proponents and utilities. TRC has reviewed hundreds of interconnection applications for utility partners, and we’ve learned important strategies for reducing the time and costs associated with interconnecting projects 1 megawatt or greater.

NERC Standard Extends Maintenance Program Obligations to Generators
February 3, 2014
The approval of NERC Standard PRC-005-2 extends protection system maintenance obligations to Generators and crates one comprehensive standard establishing minimum maintenance activities and maximum time intervals for protection systems and load shedding equipment affecting the bulk electric system.

Larry Fitzgerald
Larry Fitzgerald, CPTED, PSP, CPP leads TRC’s national Security and Emergency Management Practice, where he has supported security many different types of Critical Infrastructure, including dozens of utilities. He has assessed security, developed security master plans, security designs, developed policies, provided training, and overall security consulting/strategy for clients nationwide. Contact Larry at LFitzgerald@trccompanies.com.

Bill Hawk
Bill Hawk is TRC’s Director of Private Networks Engineering. He is a Professional Engineer with over 35 years of experience in the planning, design and implementation of all aspects of utility networks and communications systems, security systems and Smart Grid/Distribution Automation systems. His areas of expertise include technology, project planning, requirements definition, project team management and project coordination. Bill has successfully completed numerous large telecommunications and security projects with local, municipal and state utilities, governments, school districts, commercial and industrial businesses, universities and university systems. Contact Bill at BHawk@trccompanies.com.